Nine New Malware Threats that Grabbed Attention in 2010
by Fahmida Y Rashid
20 Million Strong
PandaLabs found that 20 million new strains of malware were created from January to October 2010. This is about how many were created in all of 2009. The average number of new threats created every day has risen from 55,000 to 63,000.
The Mac Attack
HellRaiser.A is a remote-control program that affected only Mac systems. PandaLabs called it “mischevious,” noting that the hacker can remotely open and close a DVD tray, open images and play videos on infected computers. It needs user permission before it can install on the computer, though.
Just Trying to Help
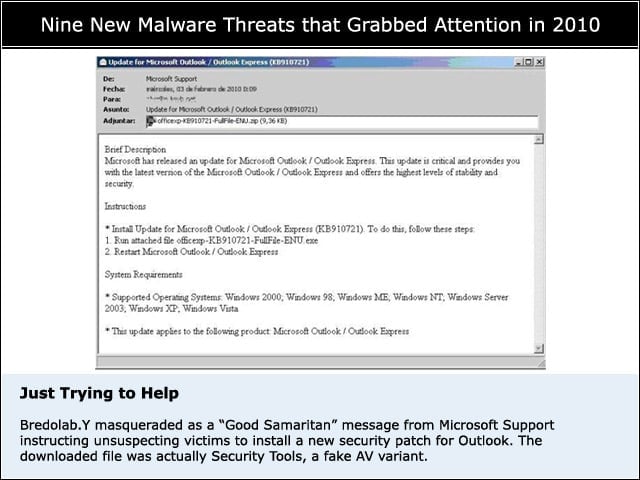
Bredolab.Y masqueraded as a “Good Samaritan” message from Microsoft Support instructing unsuspecting victims to install a new security patch for Outlook. The downloaded file was actually Security Tools, a fake AV variant.
Speaking in Tongues
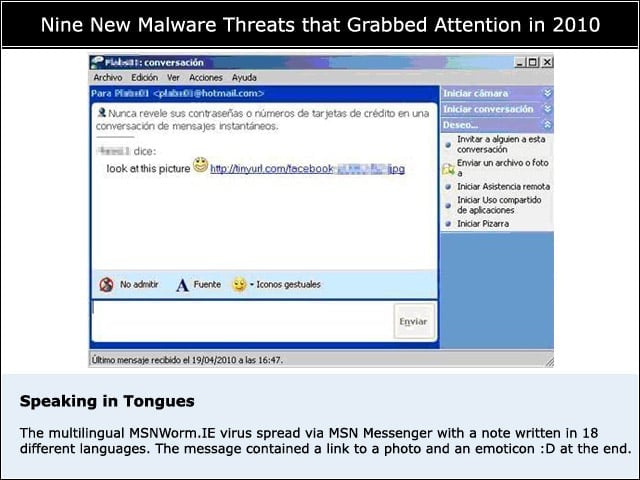
The multilingual MSNWorm.IE virus spread via MSN Messenger with a note written in 18 different languages. The message contained a link to a photo and an emoticon :D at the end.
Silent Manipulator
Stuxnet was the “most audacious” malware design, according to PandaLabs researchers, as it exploits a Microsoft USB security hole. Designed to target automated systems, Stuxnet silently manipulates PCs and process control systems, such as the ones found in Irans nuclear facilities.
Close That Pop-Up
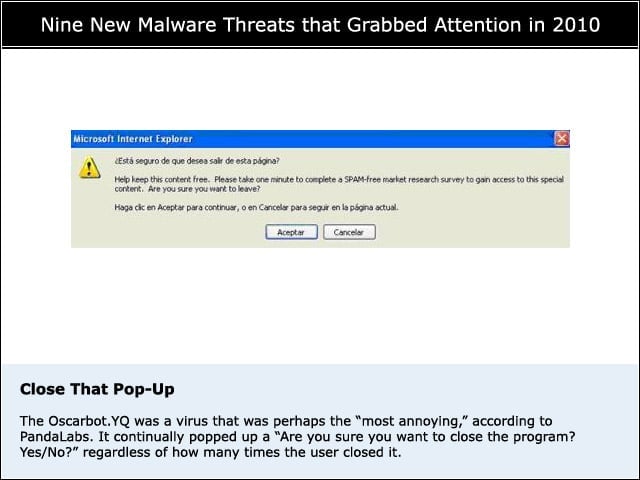
The Oscarbot.YQ was a virus that was perhaps the “most annoying,” according to PandaLabs. It continually popped up a “Are you sure you want to close the program? Yes/No?” regardless of how many times the user closed it.
A Password-Protected Virus
The Clippo.A worm gave new meaning to security-consciousness, as it password-protected all office documents on an infected system. There didnt appear to be any financial payoff with this annoying worm.
The Affordable Ransomware
Ransomware is a category of programs that block user access to their own computers and demand payment before the unlocking and releasing them. While most of them ask for $300 and up, Ransom.AB asked for only $12.
Fake AV
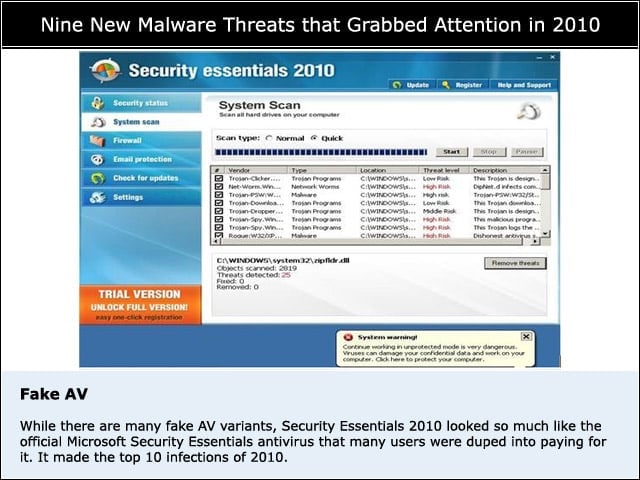
While there are many fake AV variants, Security Essentials 2010 looked so much like the official Microsoft Security Essentials antivirus that many users were duped into paying for it. It made the top 10 infections of 2010.
Gone, Not Forgotten
More than 1 million financial records were stolen using the Mariposa (Butterly) botnet before it was shut down in 2010 as a result of a team effort that brought together the FBI, U.S. Defense Intelligence, the Spanish Civil Guard and Panda Security.