Security firm Check Point today disclosed a newly discovered attack against Android devices it calls “CopyCat” that has already claimed at least 14 million victims. The Android CopyCat malware generates revenue for attackers through several mechanisms, including ad fraud and affiliate app installations.
“We called it [CopyCat] because it takes credit for installations it didn’t initiate, which is the big technological innovation it presents,” Daniel Padon, mobile threat researcher at Check Point, told eWEEK.
CopyCat has a similar type of ad fraud component as the Gooligan malware that Check Point reported in November 2016. As with Gooligan, the malware infects Android devices and then attempts to download other programs to generate affiliate commissions.
The CopyCat malware is able to inject code into Android’s Zygote application launcher to both download new applications and display fraudulent online advertisements to victims. The unauthorized application installation and fraud ads have generated approximately $1.5 million in revenue over a two-month period for CopyCat attackers, according to Check Point’s estimates.
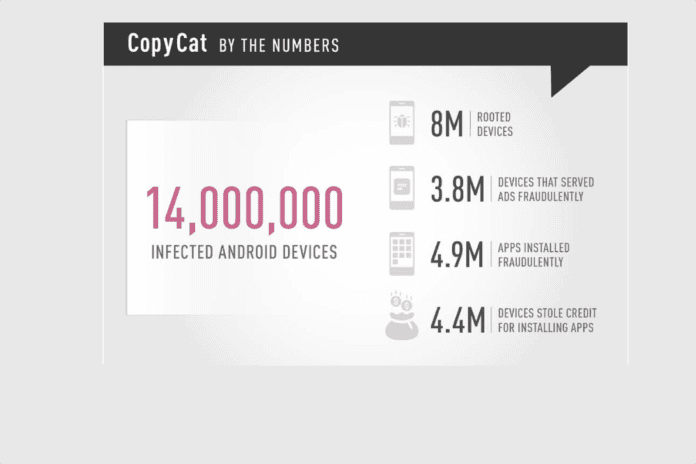
Check Point’s investigation of a command and control server behind CopyCat that was active between April and May 2016 revealed that 14 million Android devices has been infected with CopyCat malware. Of those 14 million, 8 million (54 percent) were rooted by the CopyCat malware, providing the attackers with full access to the infected devices. Check Point also estimates that CopyCat malware was able to fraudulently install 4.9 million apps on infected user devices.
Over half (55 percent) of the CopyCat infections have been in Asia, according to Check Point. In the United States, the security firm estimates that CopyCat has infected approximately 280,000 Android users.
As to why CopyCat wasn’t able to root 100 percent of the 14 million Android devices it infected, Padon provided several possible explanations. For one, fully patched devices are typically more difficult to root, though it’s not always easy to root unpatched Android devices either.
“Most rooting attempts are unsuccessful, and this is actually a significantly high success rate,” Padon said about CopyCat’s 54 percent rooting success rate. “There are many factors which fail rooting a device, even when it is not patched. Usually certain drivers are required and so on.”
Padon said Check Point informed Google of its CopyCat malware analysis prior to publishing the research today. Check Point’s analysis found no evidence that CopyCat malware was being distributed via the official Google Play Android app store.
“We usually inform Google as soon as we catch an active malware, so it can take action against it and protect users as soon as possible,” Padon said.
Sean Michael Kerner is a senior editor at eWEEK and InternetNews.com. Follow him on Twitter @TechJournalist.