Database Security, Budget Top Admins Concerns, Oracle User Survey Says
by Brian Prince
Database Security on the Menu
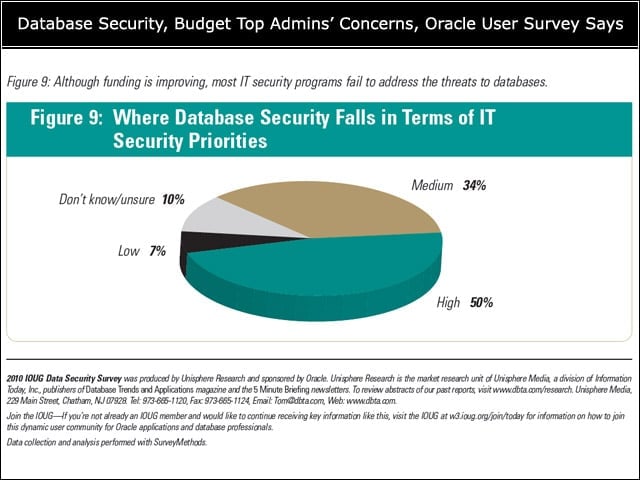
In an era of data breaches, database security is on the radar for many organizations. Still, some 17 percent of the respondents said either they don’t know how important database security is for their company or their company’s interest in it is low.
Compliance Factor
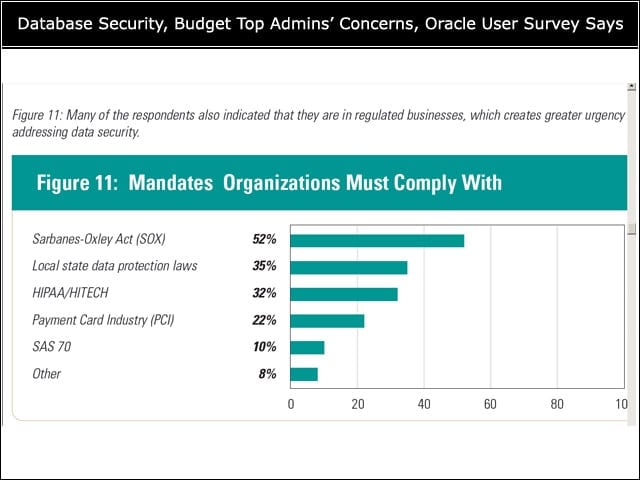
Many people said their organizations are bound by industry compliance regulations such as the Payment Card Industry Data Security Standards (PCI DSS).
Encryption Woes
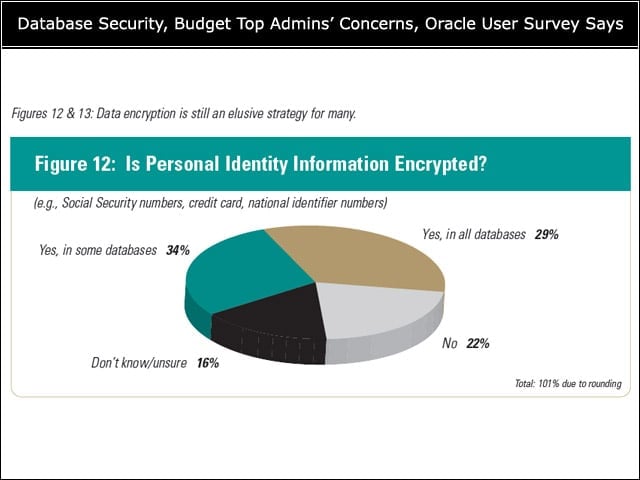
But despite the pull of compliance regulations, many organizations are not encrypting personal data or online and offline database backups and exports. In addition, 32 percent said they send unencrypted database backups or exports offsite.
Sensitive Data
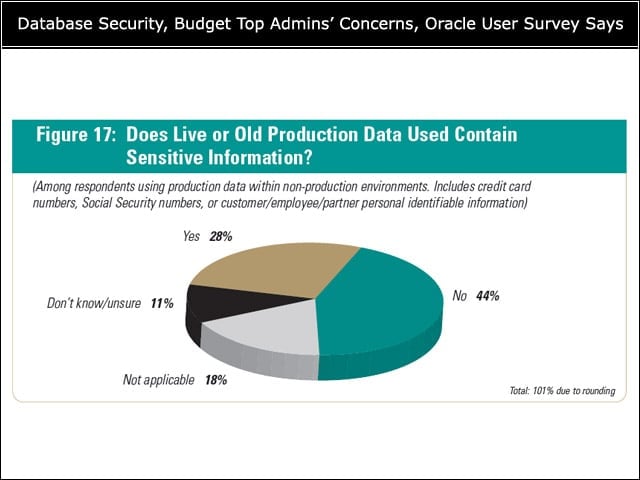
Thirty-seven percent of respondents said their organizations use live data in non-production environments. Seventy-two percent use either old information or sample data provided by the application vendor or developer, and only 28 percent said their live or old production data contains sensitive information.
De-identifying Data
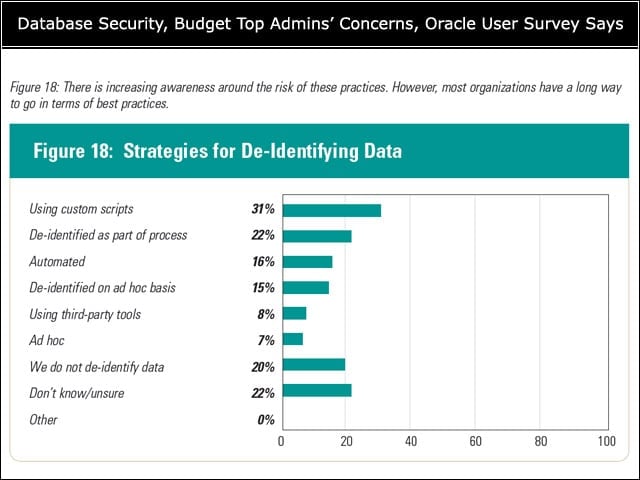
Thirty percent said they use de-identified production data in non-production environments, an increase from past years. Most, however, employ ad hoc or custom scripts to do so, something the report called “costly and error-prone.”
Wheres Waldo?
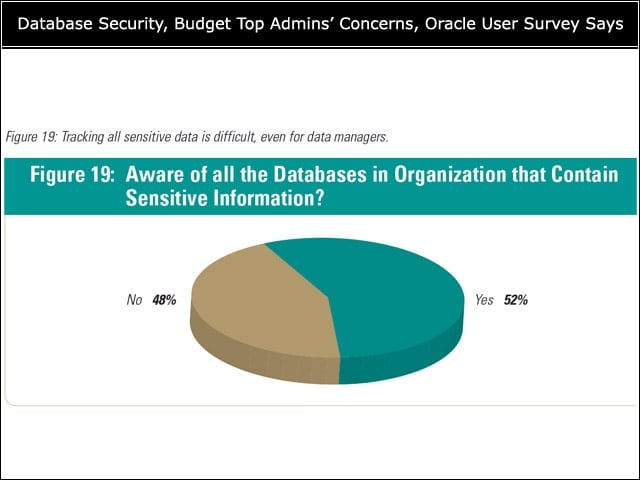
Nearly half of all respondents said they do not know how many databases in their organization contain sensitive information.
The Threat Landscape
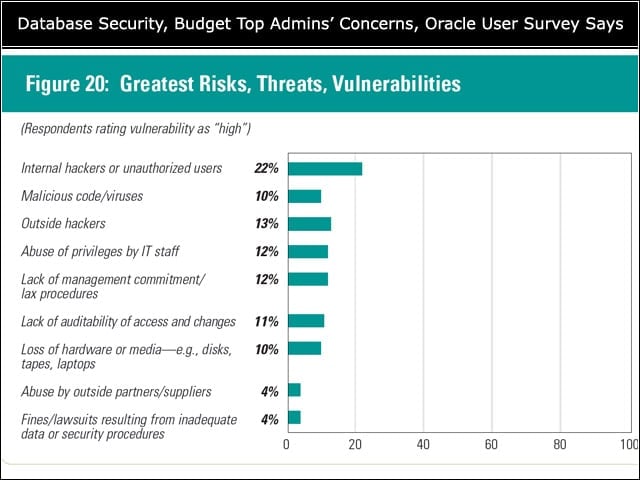
There is growing concern about insider threats due to users abusing their privileges.
Preventing Internal Abuse
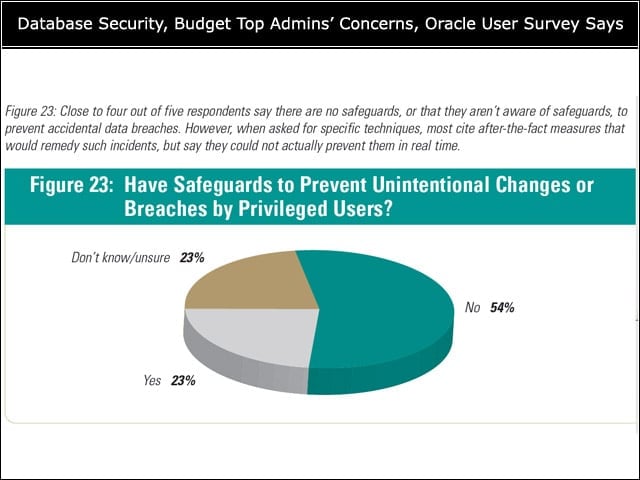
Almost 80 percent of respondents reported either there are no safeguards to protect against accidental breaches or they aren’t aware of any. When asked for specific techniques, most cited after-the-fact measures that would remedy the situation, but not prevent it, researchers found.
Database Monitoring
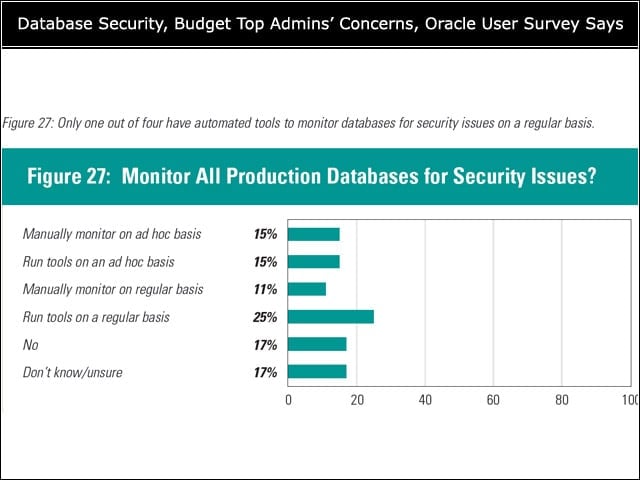
Only one in four respondents said their organizations use automated tools on a regular basis to monitor their databases. Thirty-three percent said it would take between 1 and 24 hours to detect an unauthorized change to the database. Ten percent said it would take between one and five days; 6 percent said it would take longer.
Patch Management
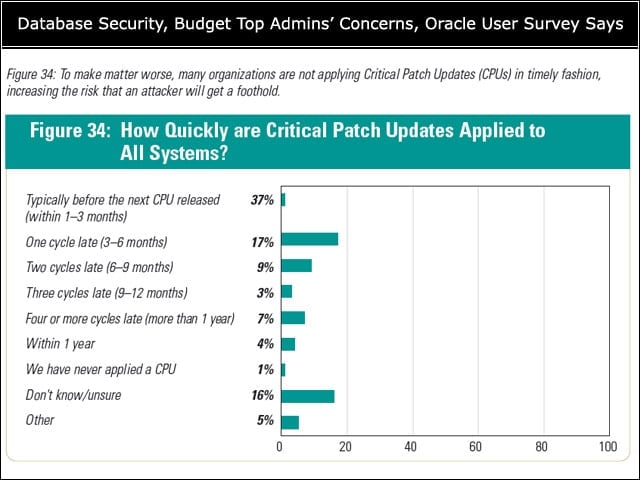
Many organizations are a step or more behind in applying critical patch updates, leaving open security holes that could be exploited by attackers.