eWEEK content and product recommendations are editorially independent. We may make money when you click on links to our partners. Learn More.
2Apps Aren’t Secure
Here’s a staggering statistic: 92 percent of the top 500 Android apps carry either a security or privacy risk, according to recent data from security firm MetaIntell. But it’s not just Android. As noted, Snapchat, among several other apps, suffers from its own security issues on iOS. At this point, it appears apps—regardless of platform—aren’t nearly as secure as one would hope.
3Follow the Hackers
Last year, in its annual security report, Sophos revealed that Android, not Windows, is the world’s most targeted platform among hackers. That report came after it was revealed that an increasing number of hackers were intentionally targeting iOS far more than all other mobile operating systems, save for Android. If the hackers are moving to mobile, both Android and iOS users should be scared—very scared.
4Communications Is a Target
Communications has become a major target for hackers around the world. In fact, over the last year or so, we’ve been hearing several reports from security firms, saying that SMS is among the top ways for hackers to break into mobile devices and steal information. The hackers achieve that by fooling mobile users into clicking on malicious links in a fashion similar to phishing in email. Be wary of communications hacks.
5For the Enterprise: Data Theft
Data theft is a major concern for the enterprise. But the concern isn’t necessarily about hackers; it’s about employees. Fiberlink, an IBM-owned company, recently told Tech Republic that the enterprise’s list of most-blacklisted apps was dominated by cloud-storage solutions like DropBox, Box and Google Drive. For the enterprise, one of the biggest threats is watching employees walk out of the office with the ability to take any sensitive data they want and put it on cloud storage.
6There’s a Hardware Element
Although much of the talk of mobile security centers on software, it’s important to point out that smartphones and tablets are, well, mobile. That means that they can be easily stolen or used in malicious ways when outside the view of the IT staff. Hardware security is a huge issue in today’s mobile-security landscape.
7Jailbreaking Is a Wild World
Although jailbreaking devices allows for access to more applications, it also opens a potential world of hurt for mobile users. In fact, the majority of security issues that affect Apple’s iOS can only harm those products that are jailbroken and not locked down. Jailbreaking allows users to run unverified apps on devices. Sometimes, that’s a good thing, but in many cases, it’s a bad thing.
8For the Enterprise: Biometric Security
There’s another problem facing the corporate world that doesn’t necessarily get the play it deserves: biometrics. While in the consumer market, biometric security, like a fingerprint scanner or the much-ballyhooed eye scanner, will help secure devices, for the IT side, it could be a nightmare. BYOD is taking the corporate world by storm. If employees are using their personal devices in the office and they’re securing those products with their fingerprints or, eventually, eye scanners, IT staff will have serious trouble gaining access to those devices and ensuring device security.
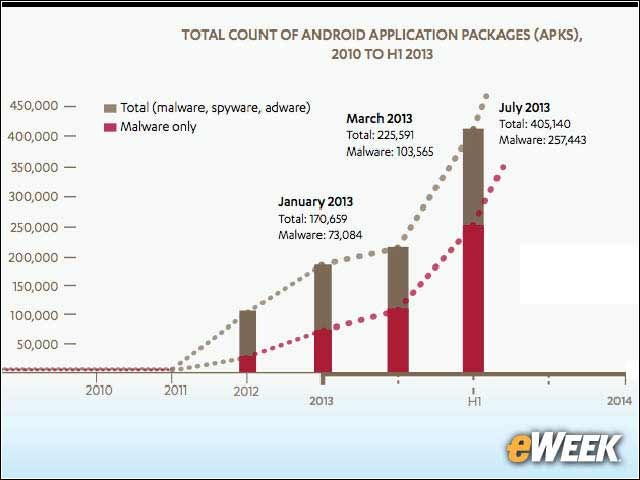
9Malware Is on the Rise
Mobile malware is expected to continue its upward trend over the next several years. Last month, McAfee reported that mobile malware was up 33 percent in 2013 compared with 2012. The company also said that it anticipates mobile malware to increase even more in 2014. At this point, it appears mobile malware is not going to slow down anytime soon.
10It’s an E-Commerce World
As last year’s Target data breach showed, malicious hackers are still more than happy to target credit cards. Historically, that has meant either targeting retailers or finding ways to steal credit card information on the PC. But now that mobile e-commerce is booming, malicious hackers are finding tricks to steal credit card information on smartphones and tablets. The e-commerce struggle continues on mobile.
11Is the Government Watching?
It would be remiss to not include some mention of alleged government surveillance as part of any discussion on mobile security. In 2013, all eyes were on the National Security Agency and other federal government agencies that have allegedly been spying on smartphones and tablets through the years. In January, a report suggested that third-party mobile advertising networks are allowing the NSA to access user data in applications and get a full dossier on individuals. Who knew the government knew so much?