[WP_IMAGE]
Open Data Center Alliance, Part 5–Security Provider Assurance The Open Data Center Alliance Security Provider Assurance usage model seeks to standardize cloud security definitions. The Provider Assurance (PA) publication is designed for use with the Open Data Center Alliance (ODCA) Security Monitoring usage model that I discussed in Part 4 of this series.
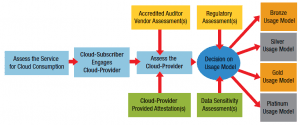
The ODCA Provider Assurance document has three stated purposes that are backed up with a four-category, bronze-to-platinum rating system. The PA model can be used to ensure that a cloud provider meets security standards. The publication also enables cloud consumers to compare security levels from one provider to another and between internally and externally hosted clouds. And finally, the PA should make it easier for cloud consumers to understand and select among various levels of security offered by providers.
The ODCA envisions that the bronze, silver, gold, and platinum ratings will be accredited by third-party certification.
The PA contains fairly specific examples laid out in check-off tables. One table outlines example security concerns, such as data protection, and then specifies at what service level that specific risk should be diminished. In this case, data protection would be assured at the “gold” and “platinum” levels, but not at “bronze” or “silver.”
A second, larger table of 25 security requirements goes into some detail about what can be expected of cloud providers. Nearly half of the requirements flow across all four of the metal-named service levels. All but eight are covered by by a silver certification. Only mandatory strong, in-flight data encryption separates gold from platinum.
The balance of the PA then covers all the factors that should be included in a responsible security review. Basic requirements for vulnerability management, network and firewall isolation, identity management, security incident and event monitoring, data retention and deletion, confidentiality, trust and availability are covered.
The one additional point that I would call out specifically is law enforcement search and seizure. For example, a cloud provider should be able to spell out exactly what level of law enforcement action is needed for the provider to turn over your data. In a private data center, there are well understood boundaries. In externally hosted environments data protections from governmental requests are much more murky.
Table of Contents for the Series:
1. IT Users Band Together: a brief introduction to the ODCA 2. Virtual Machine Interoperability 3. Carbon Footprint 4. Security Monitoring 5. Security Provider Assurance 6. Regulatory Framework 7. Standard Units of Measure for IaaS 8. Service Catalog 9. I/O Controls