eWEEK content and product recommendations are editorially independent. We may make money when you click on links to our partners. Learn More.
110 Tips to Stay Safe When You’re at Black Hat or Everywhere Else
The annual Black Hat USA security conference is underway this week, with training running from July 22 -25 and briefings on July 26 and 27 at the Mandalay Bay in Las Vegas. The Black Hat network can be a hostile one, with some researchers testing out new and old hacking skills on unsuspecting users. While Black Hat might be a more hostile network than an average corporate network, good security hygiene and best practices apply in all types of environments. The Black Hat security conference media team has offered up some tips to prevent getting “pwned” while at the show. This slide show provides 10 tips on how to stay cyber-safe during the show and while connected anywhere in the wild.
2Don’t Do Your Online Banking on the Black Hat Network
When web browsing on the Black Hat network or other public networks in the Las Vegas area, it’s a good idea not to have any expectations of privacy. Black Hat’s media teams suggest that users do not open a random website or link sent or provided by an unknown or untrusted source. Doing your online banking while online during Black Hat also is not recommended.
3Be Wary of Wireless
4Don’t Plug Into Ethernet Just Anywhere
Black Hat’s media team advises that there will be no random loose jacks or cables that will be secured outside designated Black Hat areas. As such, users should not plug into unfamiliar open line, jack, or cable. There will be no random jacks or cables that can be considered secured outside designated Black Hat areas.
5Patch All Your Hardware and Applications
6Use Encryption to Protect Sensitive Data
7Don’t Share
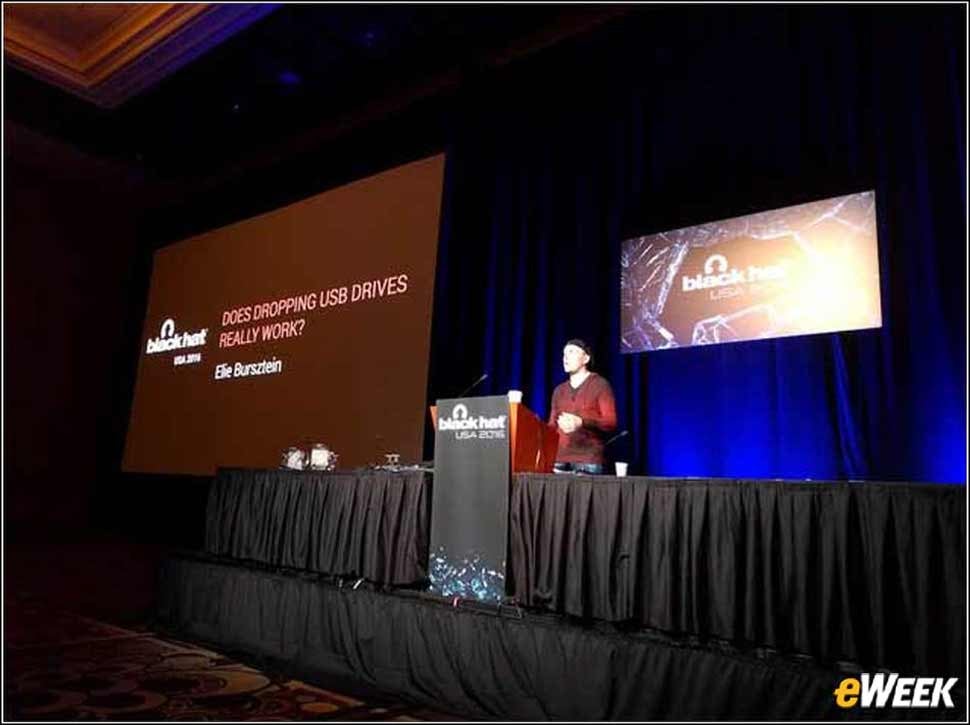
8If You Find a USB Key Do Not Pick It Up
9Don’t Use ATMs Around Conference Venue
10Protect RFID Cards
11What Happens in Vegas Stays in Vegas
Even after following the previous nine steps there are still myriad risks that could leave users exposed to future exploitation. As a best practice, the conference suggests that attendees change passwords immediately after leaving Vegas. That way any stolen passwords will stay behind in Las Vegas.