- All Data Types Are Vulnerable to Insider Theft
- Mindless Molly-Accidental Disclosure of Sensitive Information
- Self-Entitled Ernie-Claims Ownership of Organizations Information
- Cool Chris-Uses Personal Technology to Tap Corporate Databases
- Down-and-Out Dolly-Steals for Profit
- Vindictive Vinny-Taking Revenge on the Organization
- Snooping Sally-Curious About Sensitive Information
- Ideological Eddy-Exposes Data on an Ideological Principle
- Effective Ellie-Productive at All Costs
- Insiders Are Often in Technical Positions
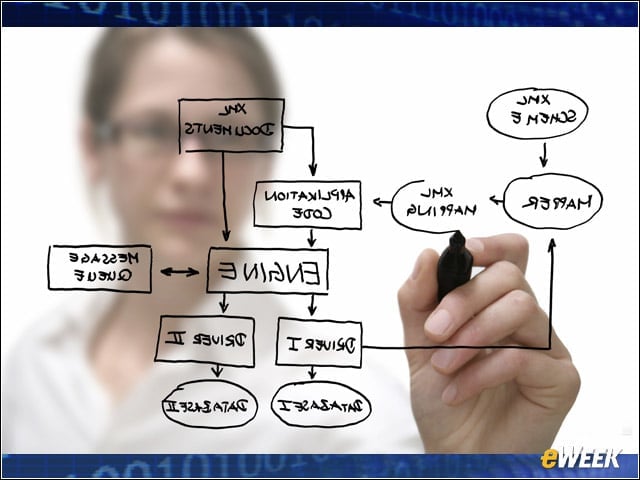
All Data Types Are Vulnerable to Insider Theft
While trade secrets are the most common type of data stolen by insiders, at 52 percent, the Symantec report found that 30 percent of breaches involve business information such as billing invoices, price lists and other administrative data. Other types of data include source code, proprietary software, customer information and business plans.
Mindless Molly-Accidental Disclosure of Sensitive Information
Mindless Molly exposes sensitive company information without even realizing it. In April 2011, a Yankees box office employee accidently sent an email attachment containing the personal information of more than 20,000 season ticket holders to recipients outside the organization. The list was widely circulated around the Web.
Self-Entitled Ernie-Claims Ownership of Organizations Information

Self-Entitled Ernie’s company doesn’t have controls that remove sensitive data from his machine, so he has accumulated a lot of it over the years. Self-Entitled Ernie considers the information to be rightfully his own.
Cool Chris-Uses Personal Technology to Tap Corporate Databases

Cool Chris uses social networks and personal devices to collaborate with others and to keep working when not at work. These tools create copies of sensitive data that exist outside of the enterprise network. An Imperva survey indicates that 80 percent of companies do not have a policy to keep corporate data off of employee-owned computers or remove collected data from personal devices after an employee departs.
Down-and-Out Dolly-Steals for Profit

Down-and-Out Dolly didn’t mean to betray the company, but times are tough and she needs the money. In 2010, a Disney employee was charged with soliciting advanced earnings reports to hedge-fund managers in exchange for money.
Vindictive Vinny-Taking Revenge on the Organization
Vindictive Vinny knows he is about to be terminated, so he sets out to sabotage his employer. In 2009, a former Fannie Mae consultant was charged with planting a logic bomb on the company’s server on the day he was fired.
Snooping Sally-Curious About Sensitive Information

Snooping Sally is authorized to access and view sensitive information, such as medical records or employee salaries. In 2011, three Tucson University Medical Center employees were fired for unlawfully accessing the health records of Tucson shooting victims.
Ideological Eddy-Exposes Data on an Ideological Principle
Ideological Eddy believes in something bigger and grander than just work. He believes in change and that his acts can lead to change, even if his bosses might not like it. In 2010, Private Bradley Manning allegedly downloaded 250,000 confidential military and diplomatic cables, which were published by Wikileaks for the world to see.
Effective Ellie-Productive at All Costs

Effective Ellie is an extremely efficient employee who keeps finding ways to be more productive, but sometimes in the race to get things done, Ellie bypasses company policies and controls she finds too restrictive. In 2010, an Imperva survey determined that 73 percent of employees believe they could easily bypass existing access control mechanisms.
Insiders Are Often in Technical Positions
The majority of intellectual property theft is committed by employees in technical positions, including engineers, scientists, managers and programmers, according to Symantec. A large percentage of these thieves had signed IP agreements, but enforcement was ineffective.