- Black Hat, Defcon Conferences: From Hackers to Pwnie Awards
- Hail Caesar! Black Hat Has Left the Building
- Keynote Makes Radical Suggestions
- Yahoo CISO Plans for Full Email Encryption
- Automotive Security in the Cross Hairs
- Heartbleed Wins a Pwnie
- Security Whac-a-Mole
- Kevin Mitnick Signs His Book
- Have a Cigar
- Hacking the Defcon Badge
- Defcon Attendees Shamed on the Wall of Sheep
- Malicious Cell Phone Chargers Appear Again
- Industrial Control System Security a Defcon Focus
- Defcon Takes Over the Penn and Teller Theatre
- WiFi Pineapple Hacking Device
Black Hat, Defcon Conferences: From Hackers to Pwnie Awards

By Sean Michael Kerner
Hail Caesar! Black Hat Has Left the Building

In 2014, Black Hat moved from Caesars Palace to the more spacious Mandalay Bay hotel and conference center
Keynote Makes Radical Suggestions
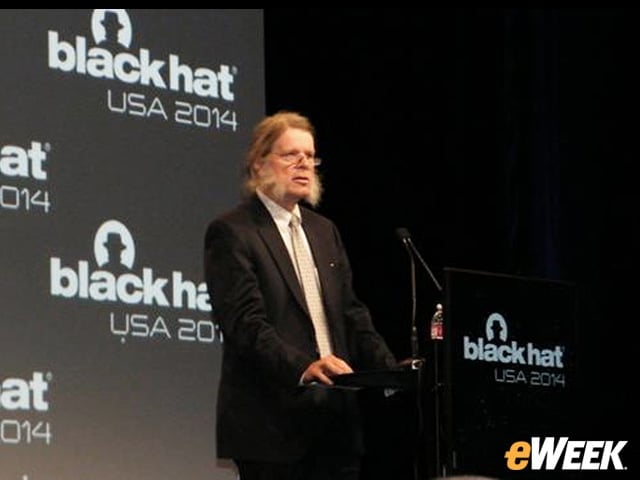
Security luminary Dan Geer was the only keynote speaker at the Black Hat USA 2014 event. In his address, he suggested that the U.S. government buy up all the world’s vulnerabilities. He also suggested that Microsoft open-source Windows XP so others could step in to support it.
Yahoo CISO Plans for Full Email Encryption
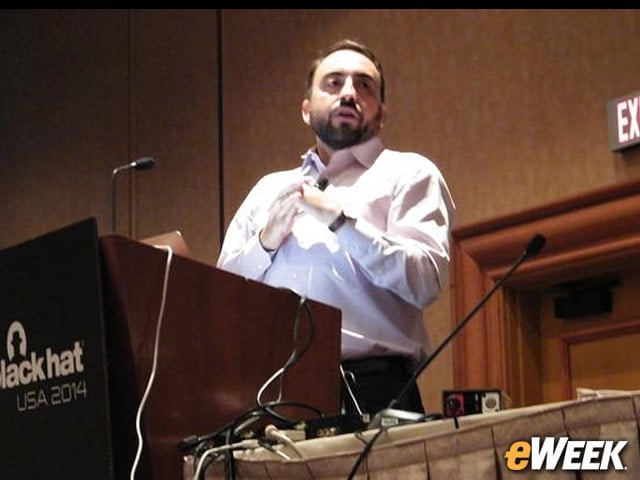
Yahoo CISO Alex Stamos used his Black Hat session as an opportunity to discuss the challenges of security at scale. He also announced a new initiative set to debut in 2015 to provide end-to-end email encryption for Yahoo Mail users.
Automotive Security in the Cross Hairs
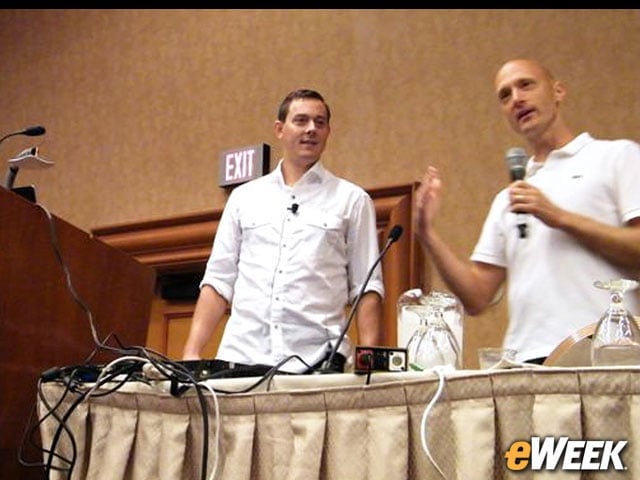
At Black Hat, security researchers Chris Valasek and Charlie Miller discussed their audit of car vendors’ security and demonstrated a new car protection device to limit risks.
Heartbleed Wins a Pwnie

At the Black Hat’s annual Pwnie award show, the Heartbleed security flaw was the winner for the Best Server-Side Bug.
Security Whac-a-Mole

The Black Hat show floor was full of interesting content and attempts to draw users. Beyondtrust had a Whac-a-Mole game in its booth.
Kevin Mitnick Signs His Book

Infamous hacker Kevin Mitnick made a Black Hat appearance. He signed copies of his book “Ghost in the Wires.”
Have a Cigar

Among the interesting giveaways was a free hand-rolled cigar from AccessData.
Hacking the Defcon Badge
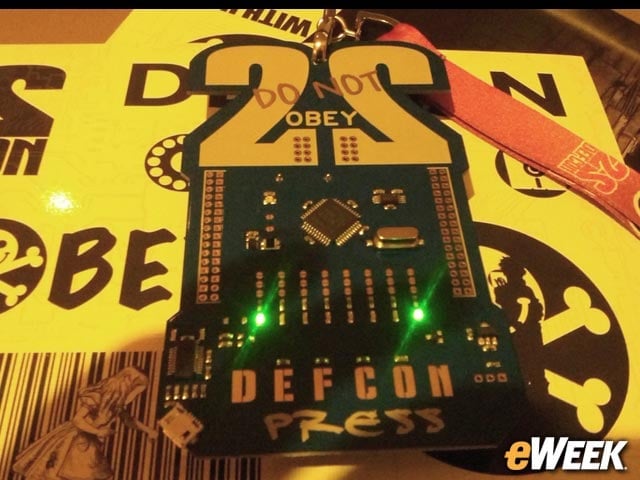
As opposed to just using a paper badge, the Defcon badge is a hackable piece of hardware.
Defcon Attendees Shamed on the Wall of Sheep

Connecting to an insecure WiFi network and sending out passwords over an unencrypted link landed a long list of Defcon attendees on the Wall of Sheep. The Wall of Sheep is an effort to teach people about the dangers of unencrypted communications.
Malicious Cell Phone Chargers Appear Again
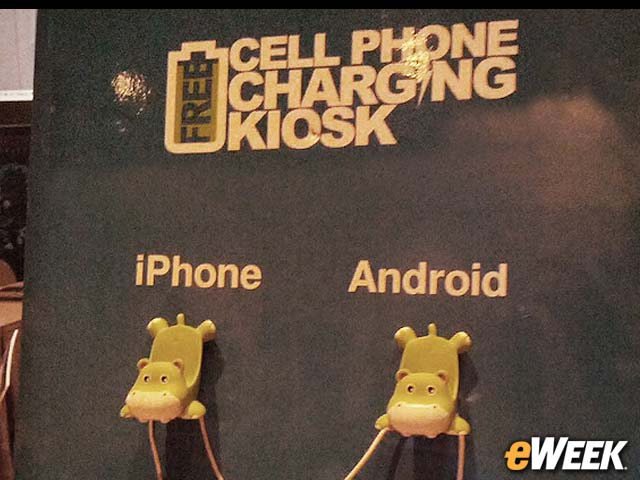
Defcon attendees were taunted by a free cell phone charger this year. USB-based connections, for power or otherwise, have been demonstrated at multiple events in past years to be security risks.
Industrial Control System Security a Defcon Focus
Among the hands-on areas at Defcon this year was the industrial control system (ICS) village, which provided attendees with the opportunity to explore industrial security.
Defcon Takes Over the Penn and Teller Theatre
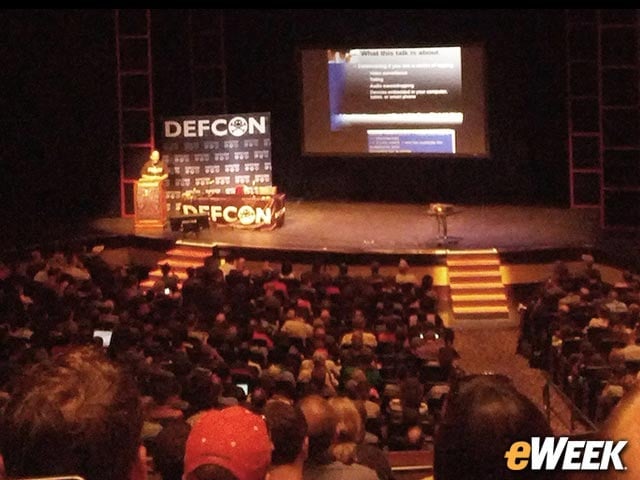
Among the venues at the Rio Hotel that were used by the Defcon conference was the Penn and Teller Theatre, which normally houses magic shows.
WiFi Pineapple Hacking Device
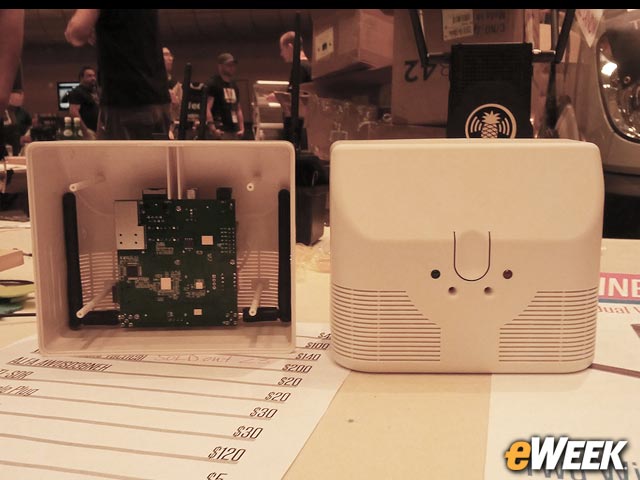
The Ominous Box looks very much like a common carbon monoxide (CO) detector, but it’s not. It’s actually a WiFi Pineapple wireless penetration testing device.








