eWEEK content and product recommendations are editorially independent. We may make money when you click on links to our partners. Learn More.
1Consumer Breaches Are Influencing Enterprise Security Policies
The consumer IT world has a lot of influence on how enterprises view cyber-security, according to Gemalto’s Identity and Access Management Index 2018 report. The 30-page report, released March 7, is based on interviews with 1,050 IT decision-makers conducted between September and November 2017. Ninety percent of respondents say their enterprise security policies for access management have in part been influenced by data breaches of consumer services. When asked about authentication, 54 percent of respondents said their work authentication is not as good as what is offered by Facebook and Amazon. In this slide show, eWEEK looks at some of the highlights of the Gemalto’s Identity and Access Management Index 2018 report.
2Consumer Services Data Breaches Influence Enterprises
3Enterprises Have Consumer Authentication Envy
While organizations’ security policies have been influenced by consumer breaches, many organizations still think that certain consumer services do a better job of authentication. More than half (54 percent) of Gemalto’s respondents indicated that the authentication systems they use at work are not as good as those offered by Facebook and Amazon.
4High Use of Social Media Credentials for Corporate Resources
5How Organizations Secure Social Media Accounts
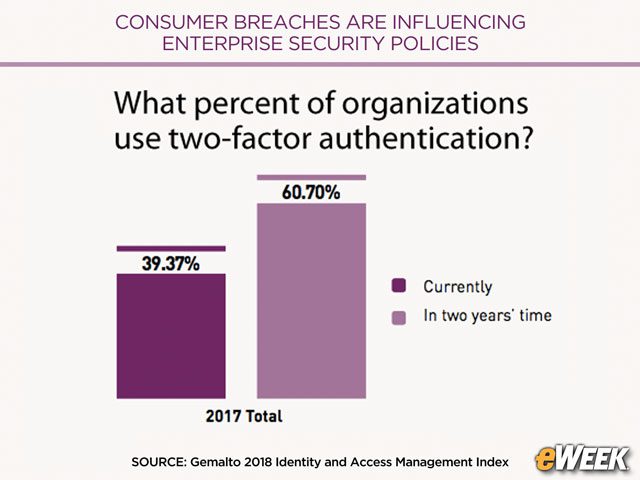
6Two-Factor Authentication Use to Grow
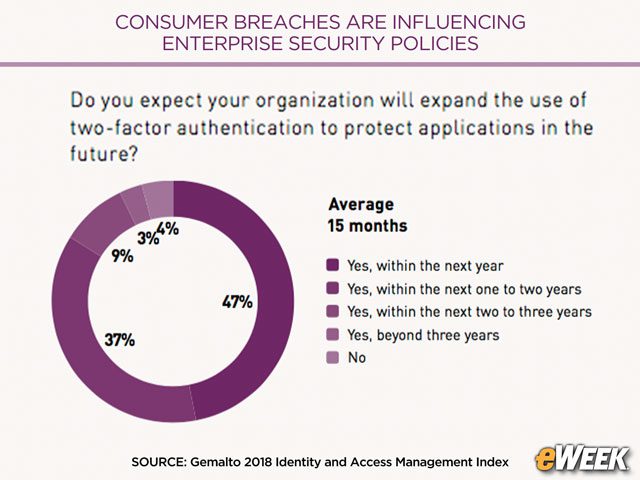
7Using Two-Factor Authentication to Protect Applications
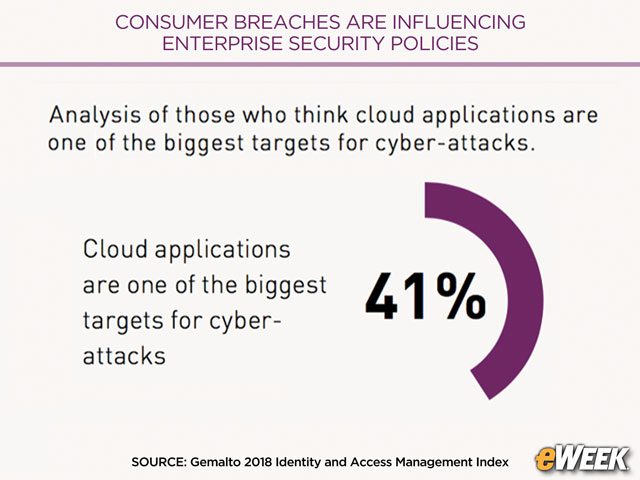
8Cloud Is a Top Target for Attacks
Forty-one percent of Gemalto’s survey respondents said that, in their view, cloud applications are one of the biggest targets for cyber-attacks. The reasons why cloud is a top target are organizations’ increasing use of the cloud and a lack of strong security.