At first glance the Copycat malware doesn’t seem like a huge threat to end users. Its primary purpose is to make money by reporting the installation of apps for which it gets paid a commission. End users will see apps installed on their Android devices that they didn’t download, and in many cases those apps will be bogus, but little else seems to happen.
But in fact, there’s a lot going on beneath the surface. Copycat, which was first discovered by researchers at Check Point Software, infects a device when the user downloads an infected app from a third-party app store or when the user falls for a phishing email. Once it’s on the device, the malware uses one of several exploits to attack the device.
The first attack is to gain root access to the Android device, which it’s able to accomplish over half the time. Once it roots the device, the malware injects code into Android’s Zygote service, which is the process that Android uses to launch apps. The Zygote attack allows the malware to download new apps silently, for which it’s paid a referral. In addition, the malware monitors user activity to get referrals for apps the user views in Google Play, for which it then also gets referral payments.
Meanwhile, the malware has installed itself to the Android system to gain persistency. Once it’s there, the user is unlikely to realize that the device has been infected and in any case the malware is difficult to remove. Unless the device is patched, the malware can stay inside the device essentially forever.
The more serious problem with Copycat is that the malware can be used to deliver payloads besides bogus ad referral requests. Because it is successful in rooting the device when it’s installed, the Copycat malware can be used to deliver some serious threats, such as ransomware, spyware or software that’s designed to infect users’ network to help spread other types of malware if it can.
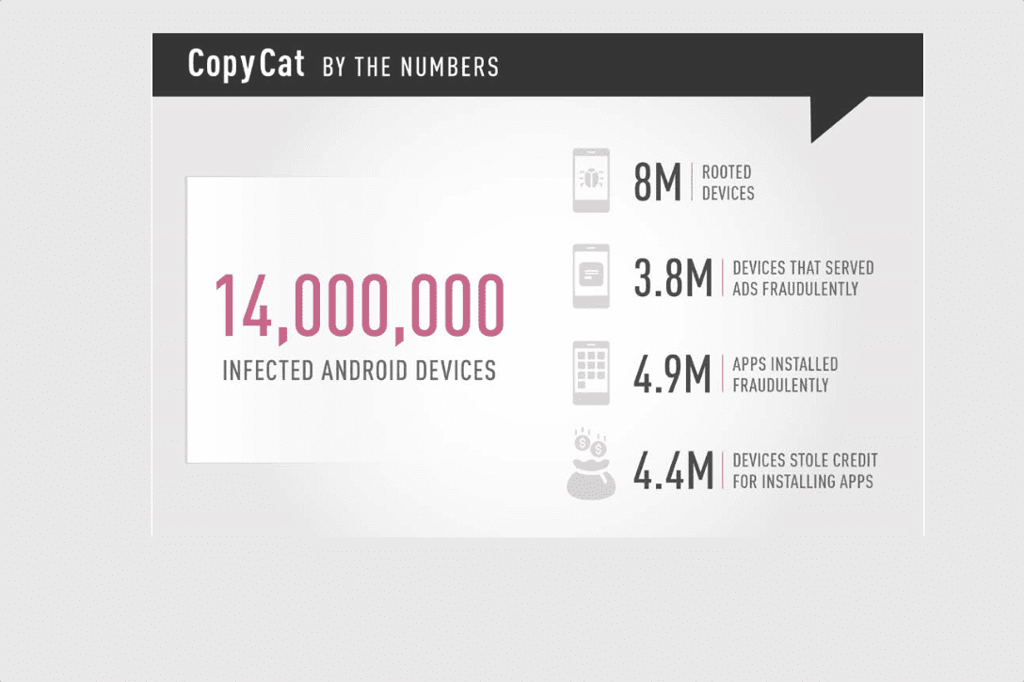
Perhaps worse, because the malware is already alive on something like 14 million Android devices, it’s entirely possible for it to install the software necessary to deliver a DDOS on a global basis, entirely using mobile devices. Because it is so distributed, such a mobile attack could proceed without being obvious to the originating networks, but could deliver a lethal blow to the target.
If there’s a positive development in all of this, it’s that Google has already issued patches for the Android devices that are affected. In addition, at this point Copycat only affects older versions of Android.
But it’s those older devices that are least likely to receive Google’s patches, meaning that the Copycat infection isn’t going anywhere anytime soon.
Much of the problem lies with device manufacturers that don’t bother to provide Android updates at all, or to stop distributing updates after a period of time—sometimes only a few months —after the device was produced. In the United States the situation is more complicated, because not only do device makers have to provide the updates, but then the carriers that service those devices have to approve the distribution over their networks.
There are ways to reduce the chances of getting malware such as Copycat on your Android devices. The first is ensure your Android devices is set to only allows apps from Google Play—especially the device is going to be used on your company network. On company owned devices, this can be permanently set.
The second is to only purchase Android mobile devices from device makers or distributors that commit to delivering security updates in a timely manner. Such a limitation will also restrict the choice of vendors and perhaps carriers or it may cost a little more, but your devices will be more secure against malware invasions.
Such a limitation may be extended to BYOD devices, meaning that you will only approve devices on your network that meet those requirements.
In addition, your employees will have to be trained to recognize phishing emails when they see them and to alert your security team if they show up. It’s likely that if one employee gets a phishing attack, others will too. This will make it possible for you to alert everyone and to recognize the malware attack when it starts.
One important training method is to create realistic simulated malware and then use it to test your staff. Perhaps you could reward employees who uncover phishing emails first.
Of course there are other methods, including the security products from the folks at Check Point Software who found the malware in the first place. There are a number of anti-malware packages that run on Android devices and it seems that every security software vendors has at least one.
In addition, your company should have network and internal defenses in place to keep malware and hackers away. Configured properly, that protection can also keep Copycat and other malware out of the network.
Ultimately, the best protection is good cyber-hygiene. Know where the devices on your network have been before you let them have intimate contact with yours. Prevent outsiders from injecting their viruses into your cyber-space. Also, don’t click on stuff that you don’t recognize or entirely trust.