Following a surge in rogue antivirus scams in 2011, the number of malicious programs disguised as security software has sunk below 2008 levels, according to data from ThreatTrack Security, an antivirus firm.
In a survey of the last five years of rogue antivirus software, the company discovered an uncharacteristic spike in the number of fake security scams in 2011, finding about 225 different malicious programs posing as antivirus software, much higher than the median of about 160. In 2012, the popularity of the scams declined even more, with ThreatTrack finding less than 150 different types of rogue antivirus software.
Part of the reason for the decline is likely that the fraudsters are more aggressively targeting users’ money using a scheme known as ransomware that forces users to pay to regain access to their system, Dodi Glenn, director of ThreatTrack’s AV Labs, told eWEEK.
“We are seeing the shift in the [antivirus] samples, where they are making the user believe that they have done something wrong and now they are required to pay to get access to their computer,” he said.
Rogue antivirus grew in popularity for much of the past decade. In 2009, antivirus firm Kaspersky Lab, for example, noted a sixfold increase in the number of rogue variants to 20,000 in the first half of 2009, compared with about 3,000 in the first half of 2008. Each fake antivirus scam, as counted by ThreatTrack, can account for thousands of variants, which are builds of the program that have minor differences to fool the victims’ defenses.
“The use of off-the-shelf solutions means that lots of similar programs can be created very quickly, and [this] also helps bypass classic signature antivirus solutions,” Kaspersky Lab stated in its blog post at the time. “There is now a production line creating rogue antivirus programs; additionally, these programs are evolving, with the body of the programs becoming increasingly sophisticated in order to prevent them from being detected by antivirus signatures.”
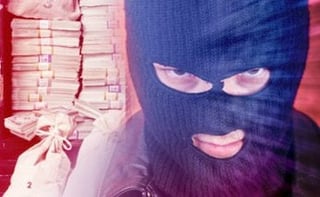
The typical fake antivirus program attempts to scare the user into installing the program—thus, the name “scareware”—by using a misleading advertisement on a Website that claims to have found infected files on the user’s system. Ransomware dials that approach up a notch: The victims’ computers are locked, and a notice is displayed that accuses the users of various crimes and telling them to pay a fine to regain access to their computer.
While ransomware has had a seeming resurgence in the past two years—with a number of ransomware schemes coming to light—the increase in ransomware is mainly anecdotal. Antivirus firms have seen the scams spread from Russia and Eastern Europe to become a global problem. The schemes can be extremely profitable, with one attack netting more than $400,000 for the criminals behind it in a single month, according to security firm Symantec.
While fake antivirus may not disappear, the lesson from the current trend is that criminals will use harsher measures to make victims pay, ThreatTrack’s Glenn told eWEEK.
“I don’t envision that fake antivirus will completely go away,” Glenn said. “I do expect that it will get more aggressive—similar to ransomware—in as much as they lock things down more and restrict the user from doing certain things, such as opening a browser.”