eWEEK content and product recommendations are editorially independent. We may make money when you click on links to our partners. Learn More.
1Data Breaches Continue to Be Financially Motivated as Detection Lags
Verizon released on April 10 the 2018 edition of its Data Breach Investigations Report (DBIR), which analyzed a filtered data set of 53,308 security incidents across multiple industries around the world. Of those security incidents, the 68-page report revealed that 2,216 were confirmed to be breaches. While the report found that there were various reasons for the breaches depending on the industry vertical, the primary motivation behind the attacks remained consistent with prior years, as Verizon once again reported that most are financially motivated. Verizon’s analysis also found that, although breaches are a known risk, 68 percent of them took months for organizations to discover. In this slide show, eWEEK takes a look at some of the highlights of the 2018 Verizon Data Breach Investigations Report.
2Breaches Are Financially Motivated
3Breach Volume Varies by Sector
4Detection Time Lags
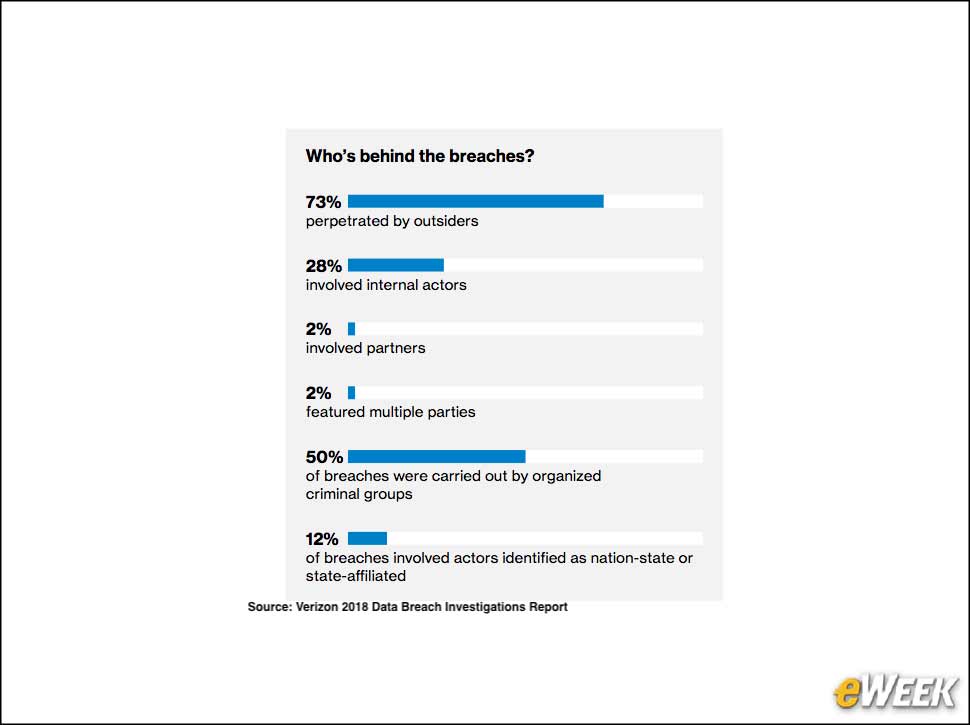
5Outsiders Are Often Responsible for Breaches
6Most Victims Are Small Businesses
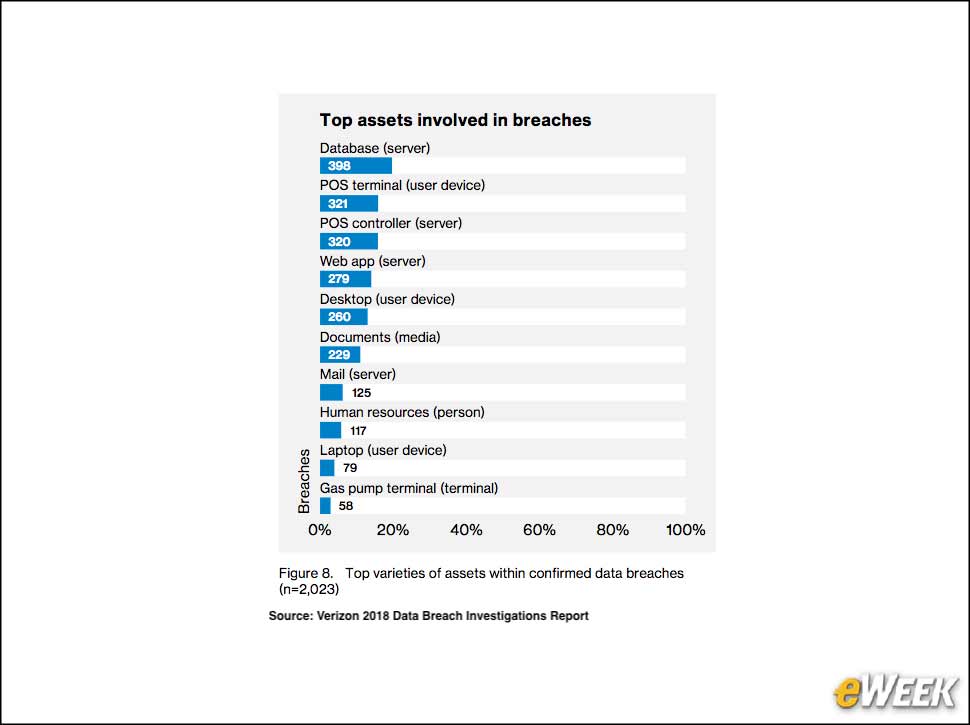
7Databases Are Often the Target
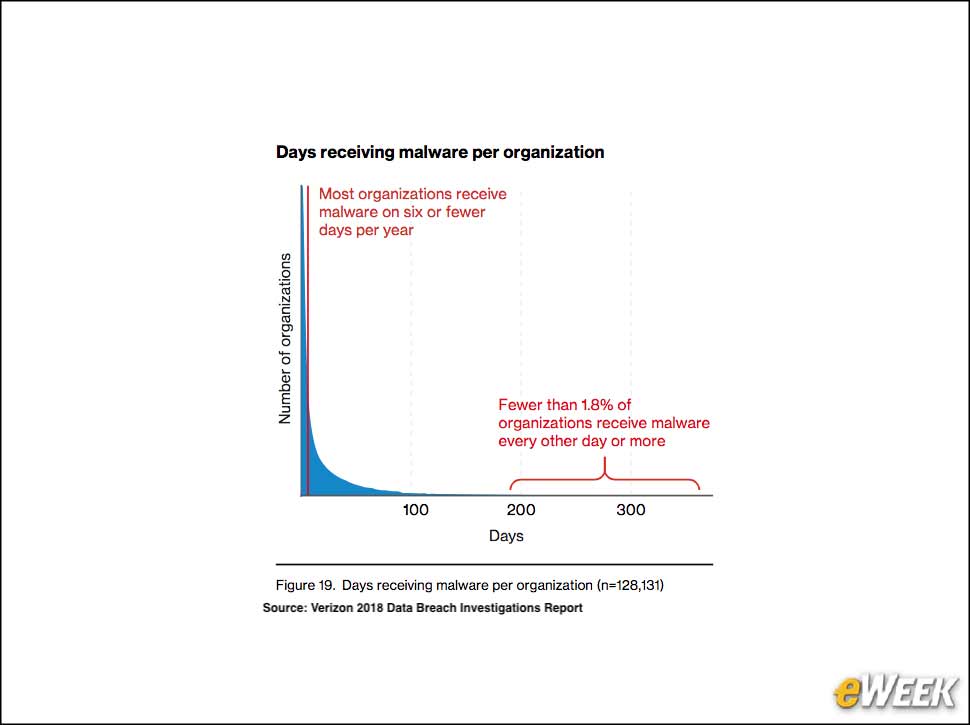
8Malware Doesn’t Hit Organizations Every Day
9Email Is the Top Malware Vector
When organizations do encounter malware, more often than not it is delivered via email. Verizon found that email is the most frequently used malware delivery model.