eWEEK content and product recommendations are editorially independent. We may make money when you click on links to our partners. Learn More.
1Encryption Use Growing for Both Data Traffic and Malware, Cisco Finds
Not only has the volume of encryption used on the internet grown in the past year, but so has its use by malware authors, according to Cisco’s 2018 Annual Cybersecurity Report. The 68-page report, released on Feb. 21, provides insight from a benchmark survey of 3,600 chief information security officers (CISOs) as well as Cisco’s own data collection efforts. According to Cisco, half of all global web traffic was encrypted at the end of 2017, a big jump from the previous year. Malware authors aren’t getting left behind when it comes to encryption either, with 70 percent of the malicious binary files analyzed by Cisco using some form of encryption. Organizations are now also using an increasing number of cyber-security vendors, which is causing orchestration challenges, according to the Cisco survey respondents. In this slide show, eWEEK takes a look at some of the key insights from the Cisco 2018 Annual Cybersecurity Report.
2Half of Global Web Traffic Is Now Encrypted
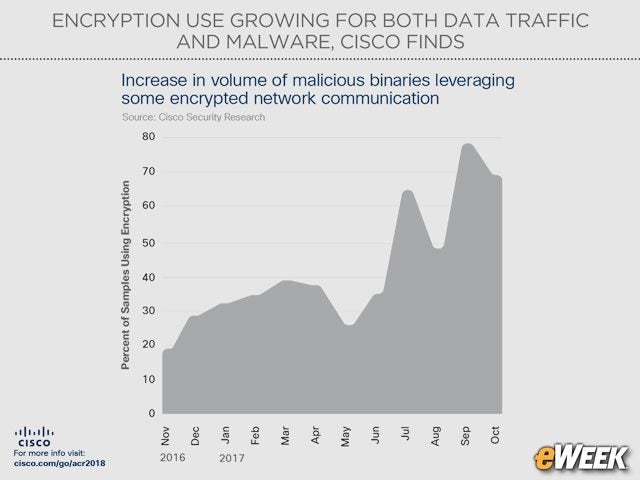
3Malware Is Encrypted Too
4Office File Extensions Top Malicious Extension List
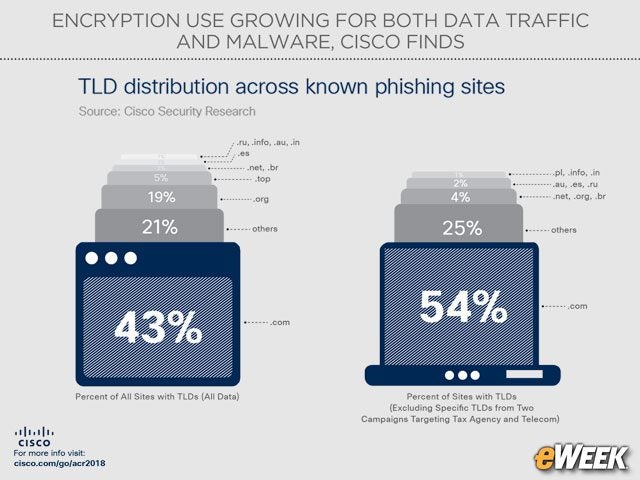
5Phishing Sites Rely on Dot-Com
6Cyber-Attacks Cost $500K or More
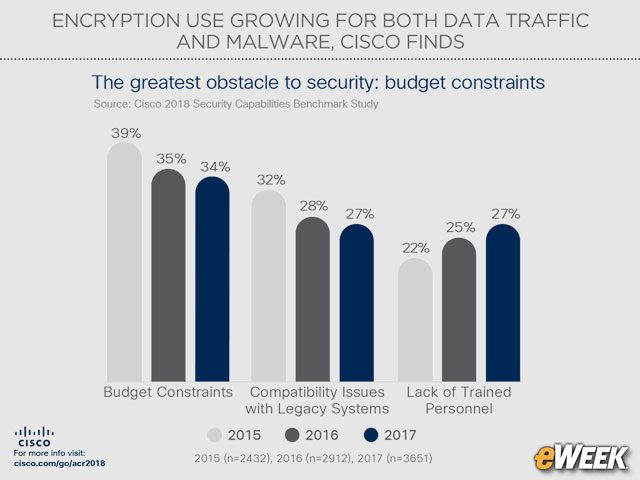
7Budget Remains a Cyber-Security Constraint
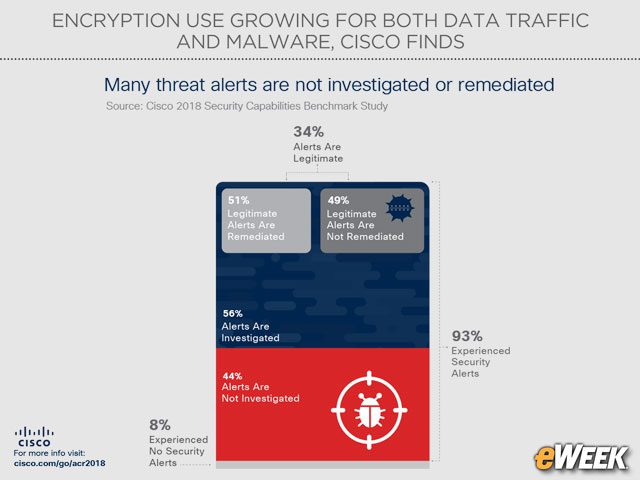
8Organizations Do Not Investigate All Alerts
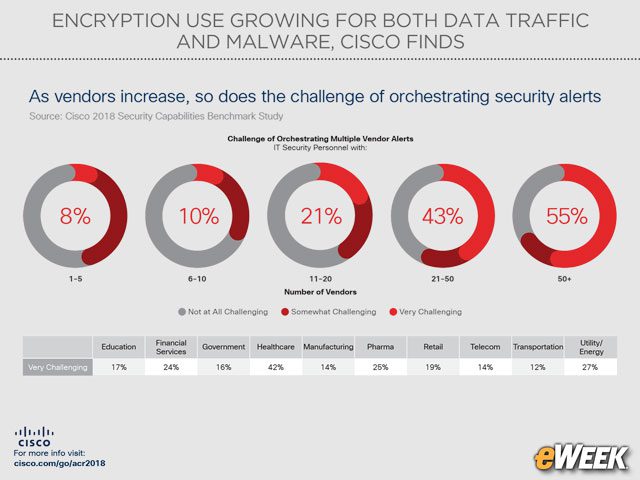
9The Challenge of Orchestrating Multiple Vendors
Cisco’s report noted that organizations are using more cyber-security products from more vendors than ever before. Twenty-five percent of the respondents reported that in 2017 they used cyber-security technologies from 11 to 20 vendors, up from 18 percent in 2016. Cisco noted that as the number of security vendors increase, so does the challenge of orchestrating security alerts.