eWEEK content and product recommendations are editorially independent. We may make money when you click on links to our partners. Learn More.
1Hackers Exploit Old Software, Trusted Websites, Menlo Security Reports
Software often has a finite lifespan, with older applications no longer receiving security and bug fix updates. However, that doesn’t mean such applications are not still in use. According to the Menlo Security 2017 State of the Web report, Microsoft’s Internet Information Services (IIS) 7.5, which was released in 2009, is still widely used, exposing organizations to vulnerabilities and the risk of exploits. The 18-page Menlo Security report was released on Feb. 5, providing insight based on an analysis of the top 100,000 websites. The top category of known bad websites that are used to make attacks or deliver malware, according to Menlo Security, are adult and pornography-related sites. The most vulnerable sites, however, are those in the business and economy category. In this slide show, eWEEK looks at highlights from the Menlo Security 2017 State of the Web report.
2Old Software Is Widely Used
3Adult Sites Are Often Used to Deliver Malware
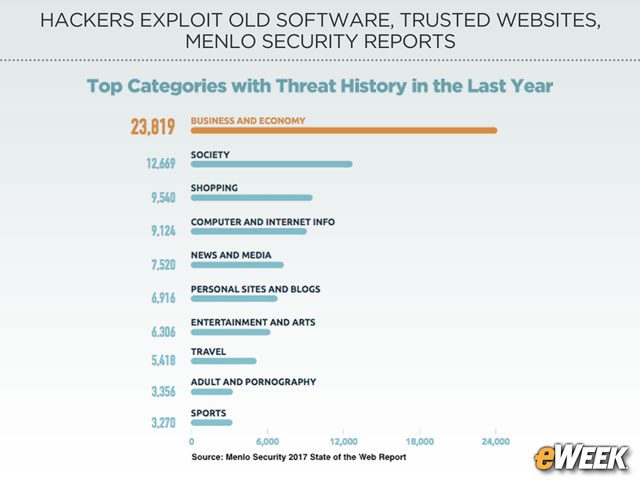
4Business Sites Are Often the Most Vulnerable
5Business Sites Are the Most Hacked
6Phishing From Safe Harbors
7Typosquatters Take Aim at Trusted Categories
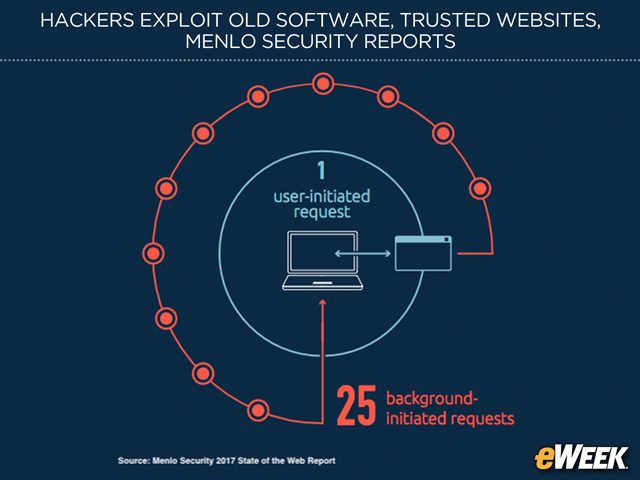
8Background Radiation Leads to Risk
Menlo Security found that most sites make background requests to other external sites to execute user requests. According to Menlo Security, every time a user visits a website, an average of 25 background requests for content are made.