IBM reported on Feb. 21 that its’ X-Force Incident Response and Intelligence Services (IRIS) unit discovered a large Business Email Compromise (BEC) attack that is responsible for approximately $5 million in losses.
According IBM X-Force IRIS, the attack is likely based out of Nigeria and has successfully targeted Fortune 500 companies. Though the source of the attack appears to be from Nigeria, IBM cautions that the new BEC campaign is unlike the so-called “Nigerian Prince” email scams that first appeared in the late 1990’s.
“While the infamous Nigerian prince email scams that have been around for decades are widely distributed at random, this campaign is extremely targeted and sophisticated, using multiple layers of social engineering tactics to evade suspicion,” Alexandrea Berninger, Security Intelligence Analyst at IBM X-Force IRIS, told eWEEK. “This Business Email Compromise attack is targeting accounts payable employees at Fortune 500 organizations and successfully stealing millions of dollars.”
Business Email Compromise (BEC) attacks aim to trick users into paying fraudulent invoices. In May 2017, the Federal Bureau of Investigation’s Internet Crime Complaint Center (IC3), reported that BEC scams have led to $5.3 billion in financial loses globally since October 2013.
Berninger explained that the new Nigerian-based BEC attack was discovered by IBM X-Force IRIS Incident Responders who investigated multiple incidents involving compromised companies. She noted that some companies confirmed they received phishing messages or they identified emails from attackers attempting to impersonate personnel, while in other cases, companies reached out to IBM after the fraud had already occurred.
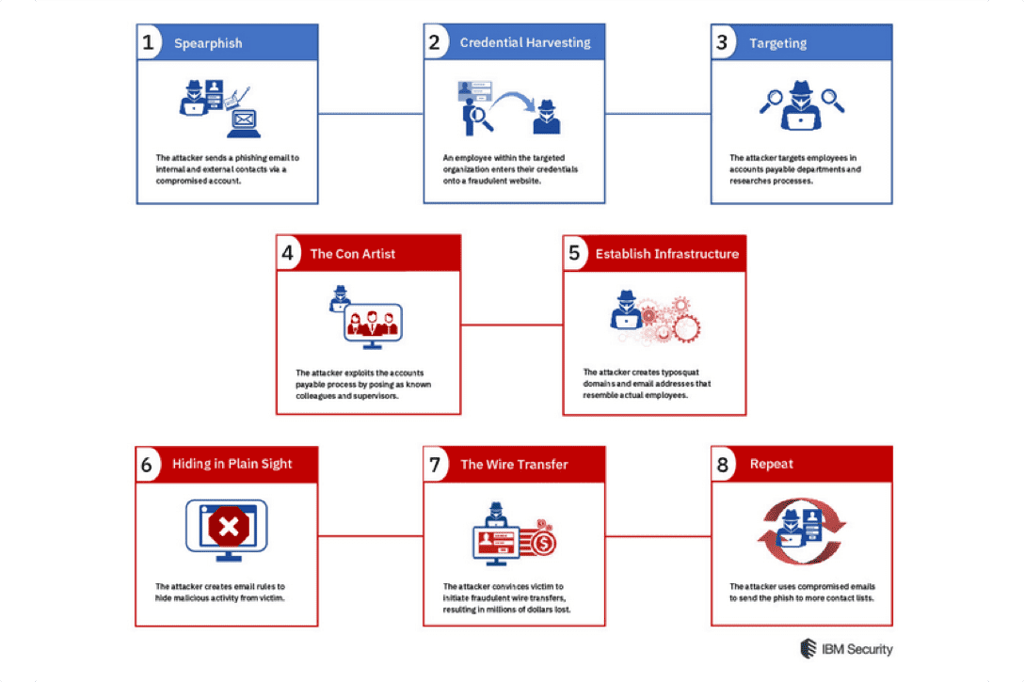
As part of the BEC campaign, the attackers were able to obtain known contacts from a target employee’s email address book in order to appear as a legitimate request. Berninger said that the BEC attackers accessed the known contacts from within the employee’s email account and sent emails directly from the victim’s email.
“Since the user’s (Microsoft) Office 365 accounts were not protected with Multi-Factor Authentication (MFA), the attacker used compromised email and password sets to directly access a victim’s email account through the web-based email service,” Berninger said.
To hide their tracks, the BEC attackers created email rules to keep the compromised account owners in the dark as to what was truly going on with their accounts. Berninger said that the attackers also created email inbox rules configured to auto-forward messages to an attacker-controlled account, so they could monitor a user’s inbox without logging into it. Going a step further, the BEC attackers made use of spoofed DocuSign login pages to get victims to pay fraudulent invoices. DocuSign is a widely used electronic signature technology that is often used alongside payment services.
“During our research we discovered that fraudulent DocuSign login pages were hosted on both legitimate (i.e. compromised websites) and malicious attacker-controlled websites masquerading as legitimate websites,” Berninger said.
DMARC Sometimes Helps Limit Risks
The use of Domain-Based Message Authentication (DMARC) is recommended as a way to help limit the risks of BEC attacks. DMARC provides integrity checks for email to make sure that it is coming from an authorized domain.
However, with the Nigerian BEC campaign uncovered by IBM X-Force IRIS, Berninger noted that DMARC wouldn’t have made a difference.
“While we do not have information to confirm whether they were using DMARC, we assess that if they had been using DMARC, the BEC campaign still could have worked, because the attackers were sending emails from within the compromised users email account,” she said.
Sean Michael Kerner is a senior editor at eWEEK and InternetNews.com. Follow him on Twitter @TechJournalist.