- Mobile Malware, Ransomware, Signed Binaries on the Rise, McAfee Finds
- Signed Malicious Binaries on the Rise
- New Mobile Malware Still Growing
- Mobile Malware Wants to Know About You
- Ransomware Samples Doubled Year-Over-Year
- New Rootkit Malware on the Decline
- Most Network Attacks Target the Browser
- The U.S. Is the Top Spam-Hosting Nation
- Cutnet is the World’s Top Spam Botnet
Mobile Malware, Ransomware, Signed Binaries on the Rise, McAfee Finds
by Sean Michael Kerner
Signed Malicious Binaries on the Rise
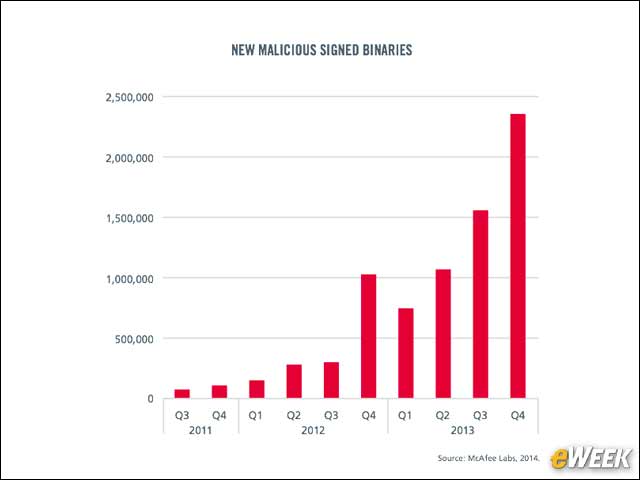
Malicious binaries increased over the course of 2013, particularly during the fourth quarter, McAfee Labs observed attackers digitally signing their code in an effort to trick users into thinking it was legitimate.
New Mobile Malware Still Growing
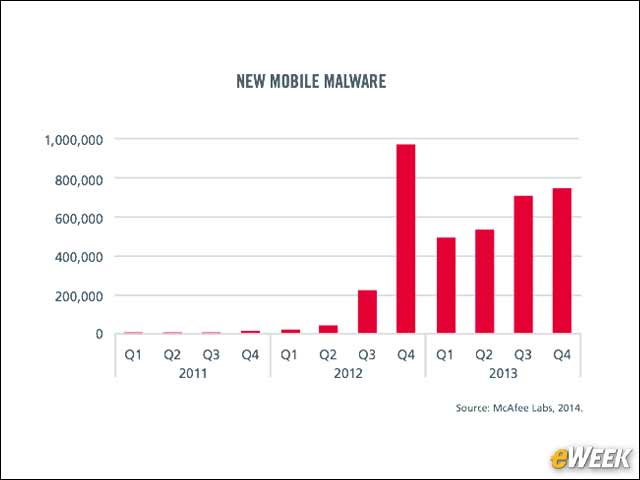
Mobile malware continues to be a growing concern, though McAfee Labs reported fewer new mobile malware samples in the fourth quarter of 2013 than during the fourth quarter of 2012.
Mobile Malware Wants to Know About You
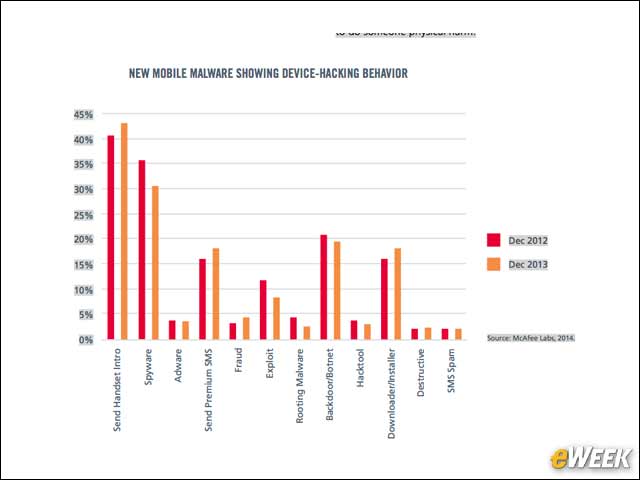
Mobile malware has many different behaviors. The top behavior is to simply collect and send device telemetry and information without the mobile user’s knowledge or authorization.
Ransomware Samples Doubled Year-Over-Year
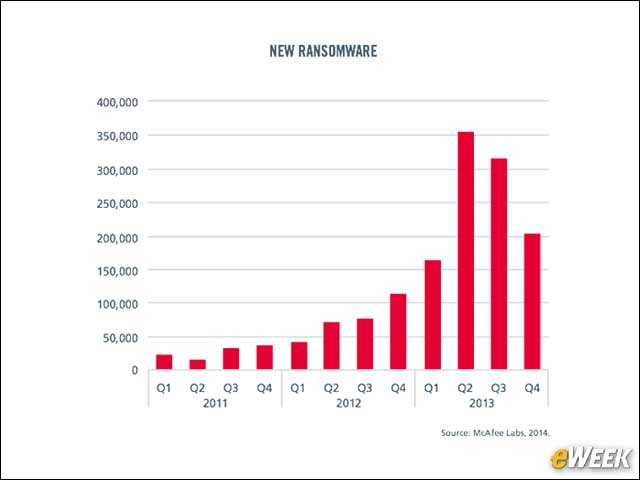
Malware that holds users’ devices hostage for ransom (hence the term “ransomware”) became a significant problem in 2013. McAfee Labs reported that new ransomware samples doubled year-over-year in the fourth quarter.
New Rootkit Malware on the Decline
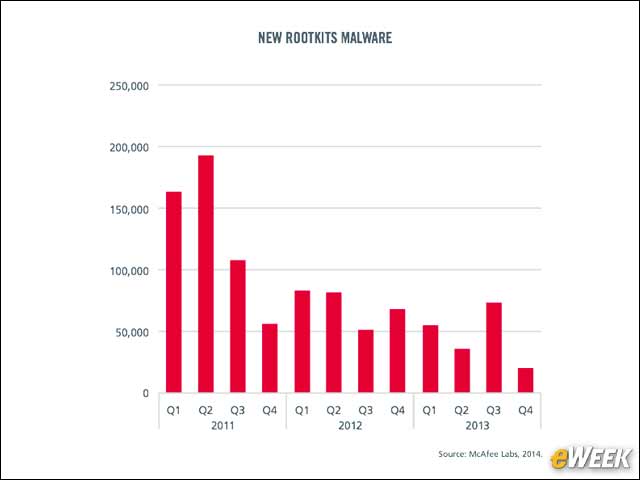
Not all forms of malware are growing. McAfee Labs reported that rootkit malware—which is activated at the time an operating system boots up—is on the decline. In the fourth quarter, Rootkit malware declined 73 percent year-over-year.
Most Network Attacks Target the Browser
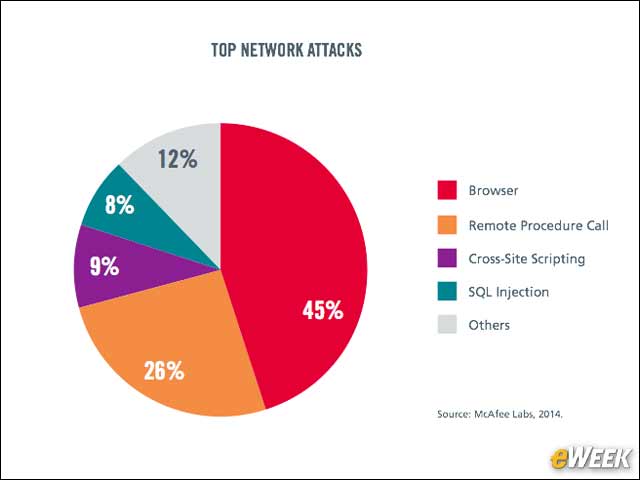
According to McAfee Labs, the leading targets for network-based attacks are Web-browser vulnerabilities.
The U.S. Is the Top Spam-Hosting Nation
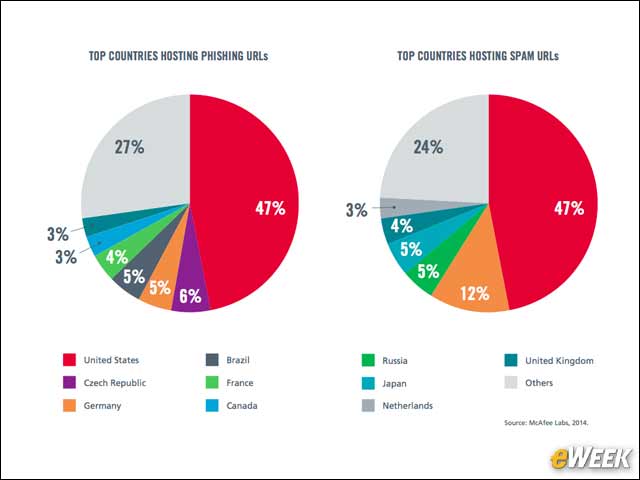
When it comes to identifying the location of where phishing and spam Web addresses are located, the U.S tops the list.
Cutnet is the World’s Top Spam Botnet
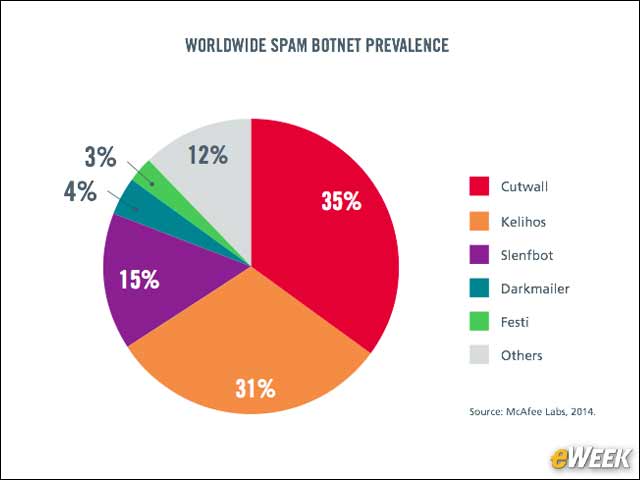
While the U.S. is the top nation for spam-hosting Web addresses, the Cutwall is the most prevalent spam botnet followed closely by Kelihos.








