eWEEK content and product recommendations are editorially independent. We may make money when you click on links to our partners. Learn More.
1Organizations Failing to Implement Planned Cyber-Security Strategies
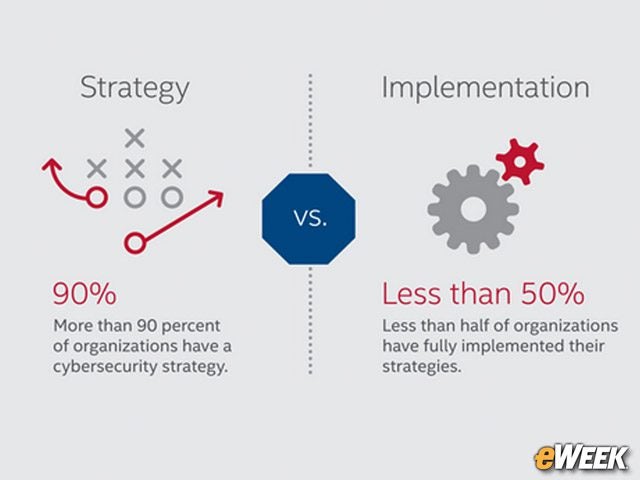
There are multiple gaps in the perception and reality of cyber-security between corporate executives and the IT professionals responsible for implementation, according to findings by Intel Security. Intel Security and the Center for Strategic and International Studies (CSIS) came to that conclusion in a 34-page report titled “Tilting the Playing Field: How Misaligned Incentives Work Against Cybersecurity.” The study surveyed 800 cyber-security professionals around the world, including both operators and executives, to gain insight into the current perceptions of the risks and the rewards of the IT security industry. One of the top findings in the report was that while 90 percent of organizations said they have some form of cyber-security strategy in place, the reality is that less than 50 percent of organizations have actually implemented the planned cyber-security strategy. Also, the study found that 54 percent of respondents were more concerned about the impact a security breach will have on their reputations than the actual impact of the security incident. In this slide show, eWEEK takes a look at some of the key highlights of the report.
2Organizations Fall Short When Implementing Their Cyber-Security Strategies
3Reputation Impact Is More Important Than Security Impact
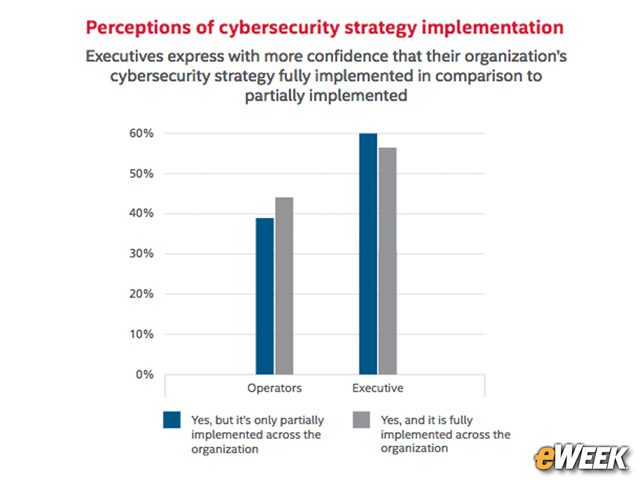
4Operators and Executive Have Different Views
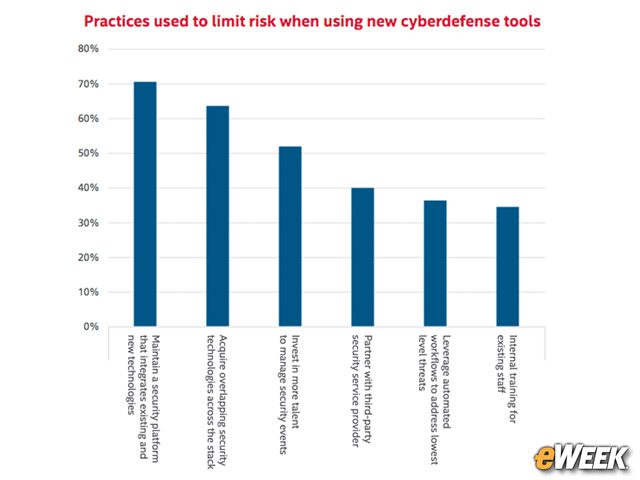
5Organizations Use Overlapping Sets of Security Capabilities
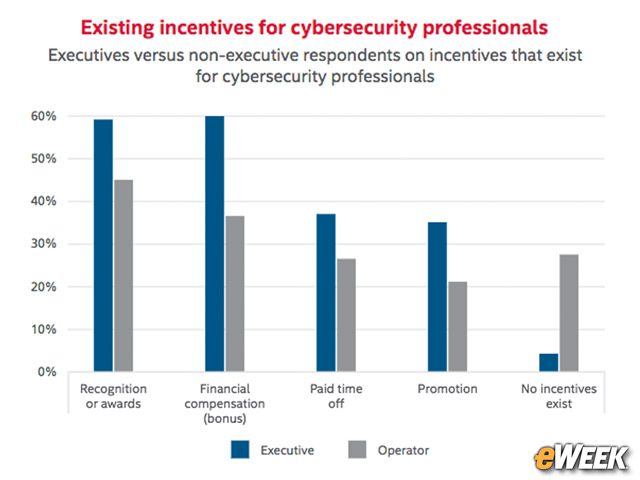
6Cyber-Security Incentives Vary
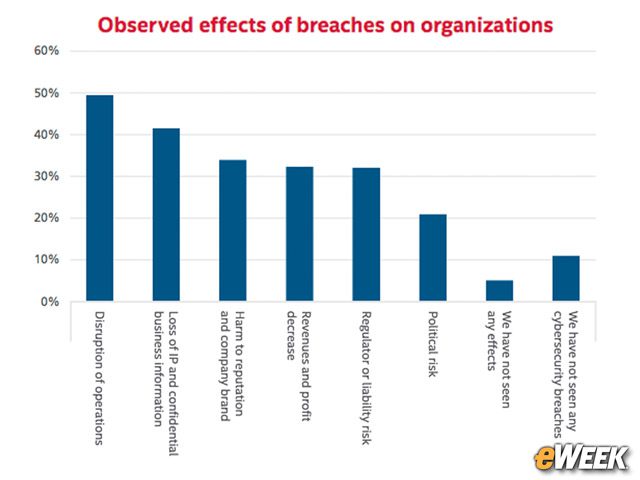
7Breaches Impact Operations
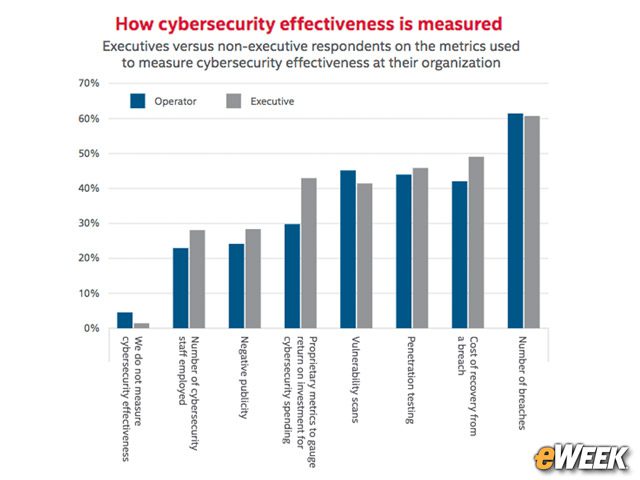
8Breach Prevention Is a Key Measure of Effectiveness
When it comes to rating the effectiveness of cyber-security, both IT executives and operators largely agree that minimizing the number of security breaches is a primary metric.