eWEEK content and product recommendations are editorially independent. We may make money when you click on links to our partners. Learn More.
1PoS Attacks on the Rise and Spam Rebounds, Trustwave Reports
Security services firm Trustwave released its 92-page 2017 Global Security Report on June 20, providing insight into security trends observed by the firm from data breach investigations conducted around the world. One trend was a growing volume of point-of-sale (PoS) system breaches, which grew to 31 percent of breached environments analyzed by Trustwave in 2016, up from 22 percent in 2015. “Cybersecurity in 2016 had both highlights and lowlights,” Trustwave CEO and President Robert J. McCullen said in a statement. In this slide show, eWEEK looks at both the highlights and the lowlights of the 2017 Trustwave Global Security Report.
2PoS Attacks Growing
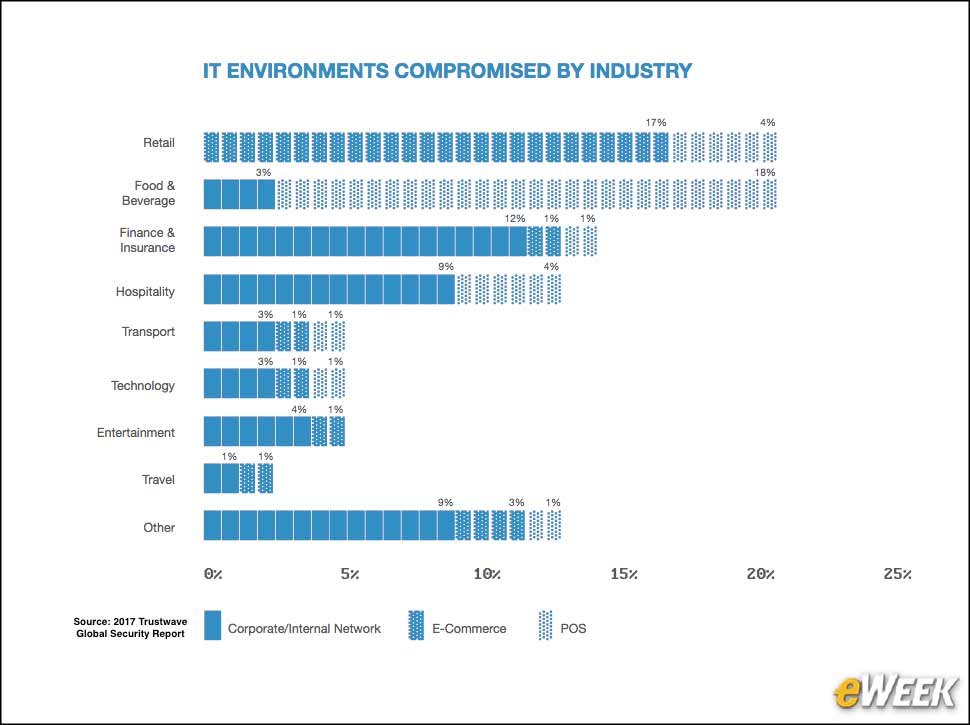
3IT Environment Compromises Vary by Industry
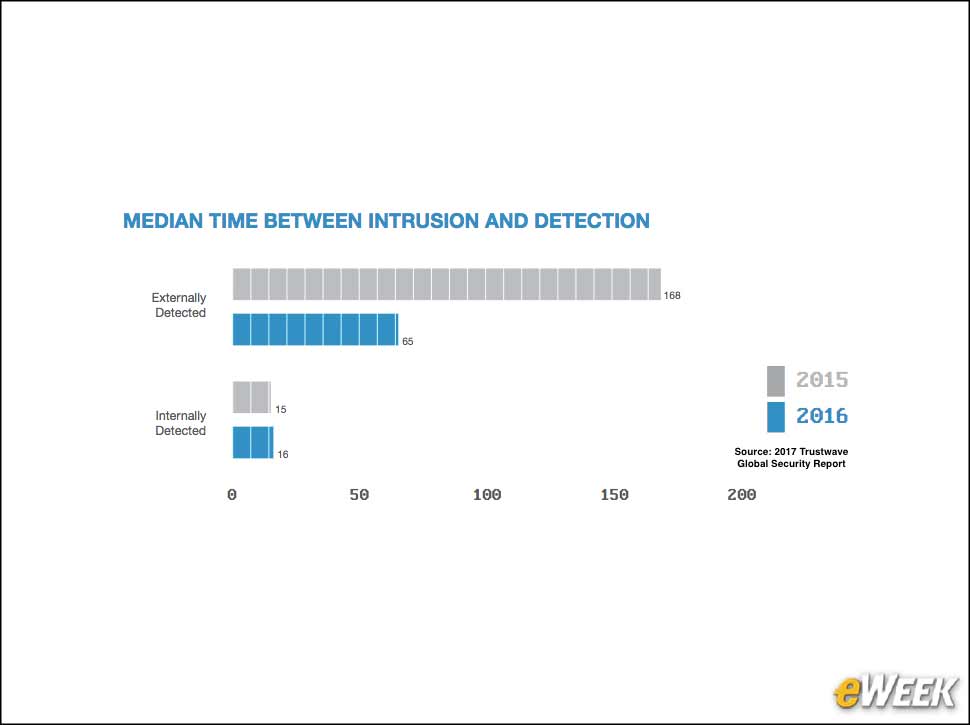
4Time to Detection Declined
5What’s Faster, Internal or External Breach Detection?
The time it takes for an organization to discover an intrusion is typically significantly faster when the organization is able to detect a breach on its own. According to Trustwave, the median time between an intrusion and internal detection was 16 days in 2016. In contrast, if the breach was externally detected, the median was 65 days.
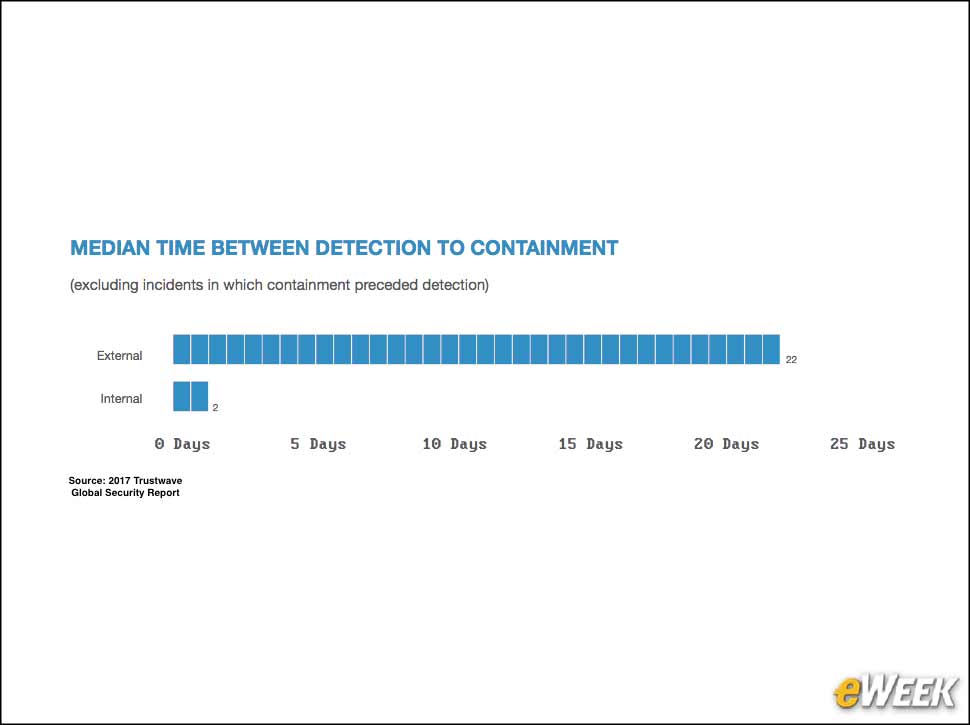
6Breach Containment Slower When Intrusion Is Externally Detected
7XSS Is the Leading Web Attack
8Penetration Testing Reveals Authentication Bypass Risks
As part of its penetration (pen) testing engagements, Trustwave was able to discover different critical vulnerabilities. The most common vulnerability discovered through pen testing was authentication bypass flaws, which enable attackers to get access to a system or application without being properly authenticated.
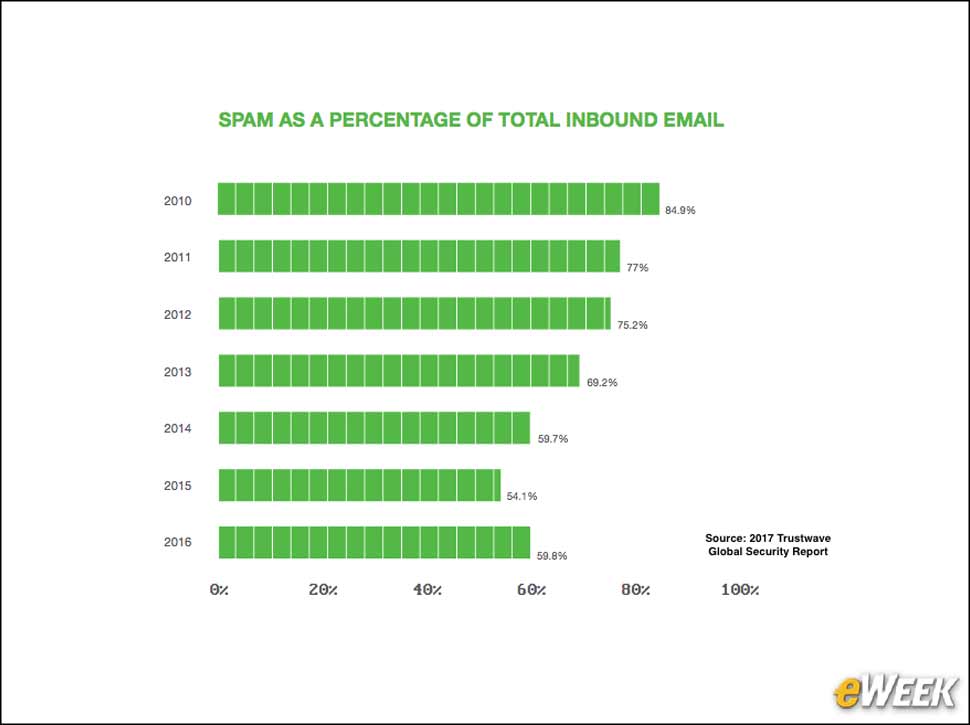
9Spam Rebounds
After a steady decline in spam from 2010 to 2015, Trustwave reported that the trend changed direction in 2016. According to Trustwave’s analysis, 59.8 percent of all inbound email was spam in 2016, up from 54.1 percent in 2015.