Security Picture Shows Less Spam, Java as Top Exploit

by Sean Michael Kerner
Spam Volumes Fall Sharply
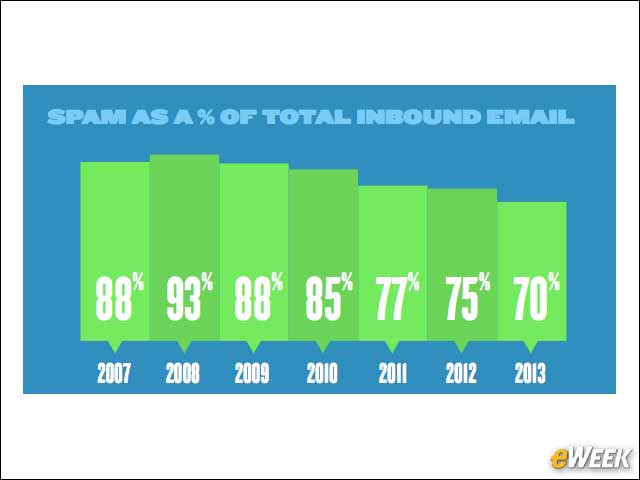
Spam as a percentage of total in-bound email is on a downward trend, declining from 93 percent in 2008 to 70 percent in 2013.
U.S. Is Top Source of Attackers and Victims
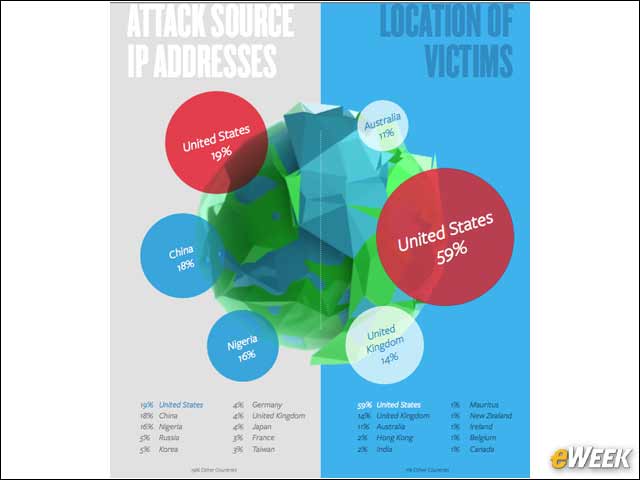
The United States is the most attacked country, with 59 percent of all victims, and it’s also the top source of attacking IP addresses, at 19 percent.
‘123456’ Is a Popular Password
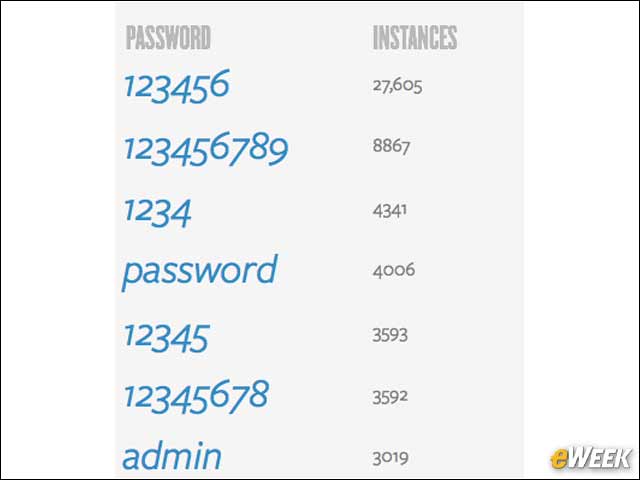
Trustwave examined passwords from users that were victims of the Pony botnet and found that the password “1234567” was the most popular.
Java Is the Top Exploit
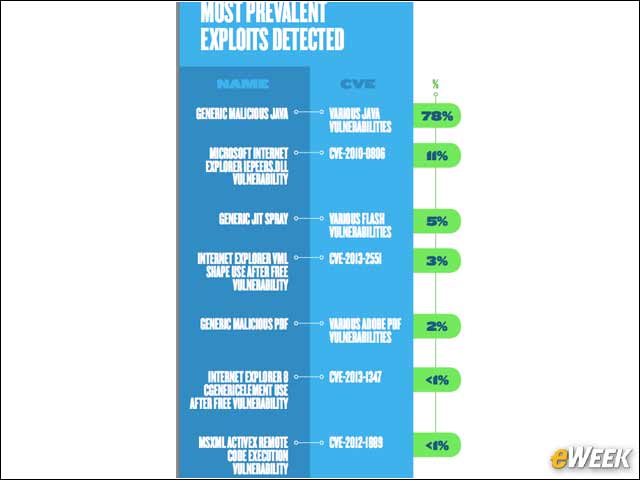
Java vulnerabilities top the list of the most prevalent exploits detected by Trustwave, representing 78 percent of exploits in 2013.
Median Time From Intrusion to Containment Is 114 Days
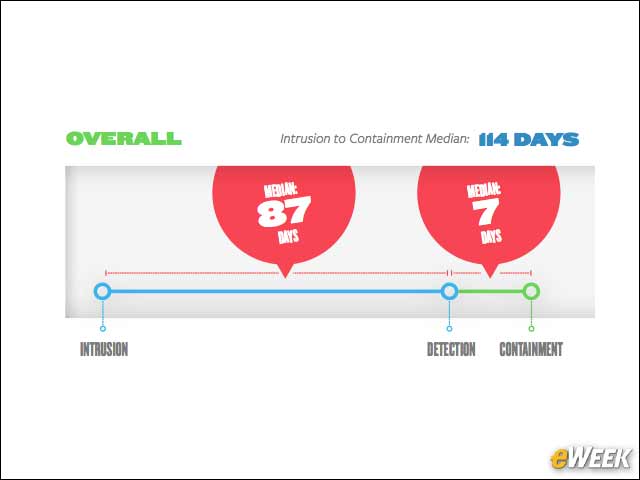
According to Trustwave, the median time it took organizations to detect an intrusion was 87 days. Overall, the median time from intrusion to containment was 114 days.
Weak Passwords Invite Intrusion
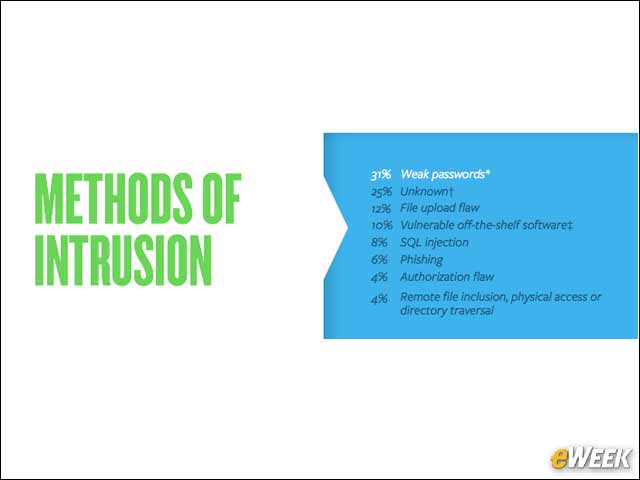
Trustwave reported that 31 percent of the intrusions it investigated were initially a result of weak passwords.
Are Organizations Detecting Breaches?

Only 29 percent of organizations detected a breach on their own, the study shows.








