- Seven Surprising Trends from HP’s Security Risk Report
- Total Number of Disclosures Grew in 2013
- ZDI Bought More IE Flaws Than Any Other Product
- SCADA Submissions Are Up
- Mobile Apps Provide Unnecessary Permissions
- Encryption: The Leading Mobile App Security Issue
- Trojans Dominate the Android Malware Landscape
- Software Is Leaking Information
Seven Surprising Trends from HP’s Security Risk Report
by Sean Michael Kerner
Total Number of Disclosures Grew in 2013
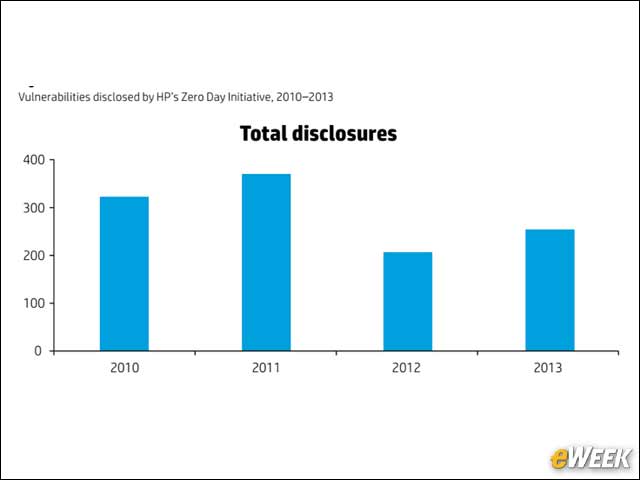
The volume of vulnerabilities reported by HP’s Zero Day Initiative (ZDI) increased in 2013 from 2012, though still did not reach the high point achieved in 2011.
ZDI Bought More IE Flaws Than Any Other Product
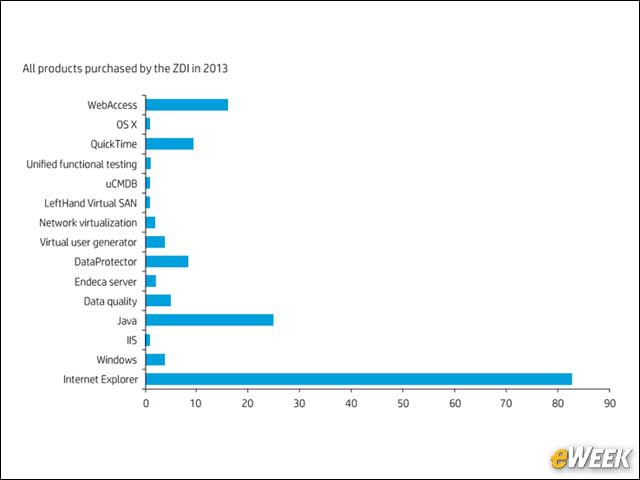
ZDI acquires all manner of software vulnerabilities; though in 2013, Microsoft’s Internet Explorer was the clear leader. Jacob West, CTO of enterprise security products at HP, told eWEEK: “IE is the most prevalent browser on the systems that attackers want to compromise.”
SCADA Submissions Are Up
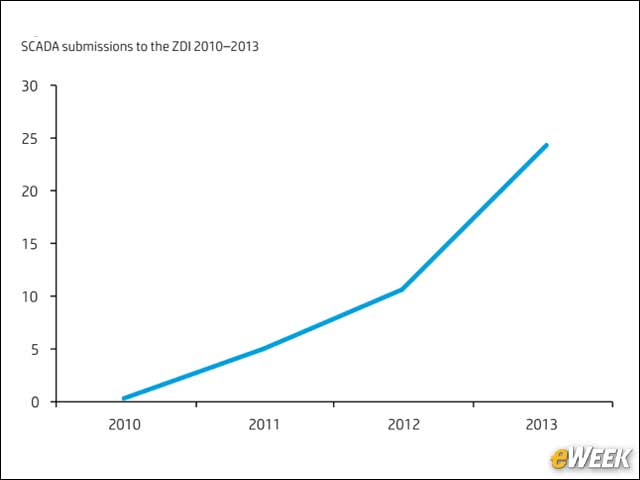
Supervisory control and data acquisition systems play a critical role in industrial infrastructure. HP has noticed a trend in recent years with an increasing number of SCADA vulnerability submissions.
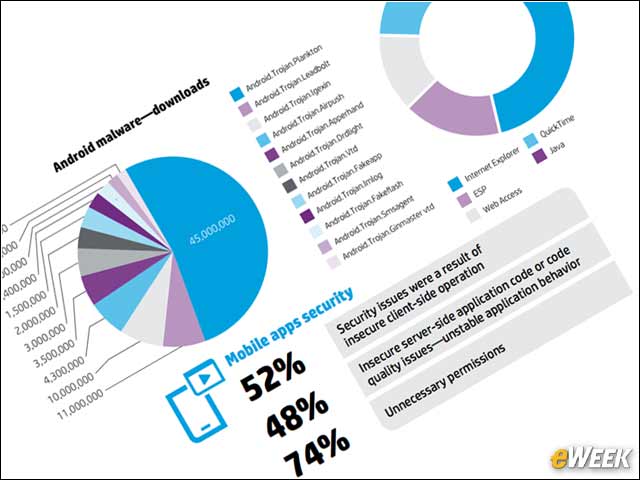
Mobile Apps Provide Unnecessary Permissions
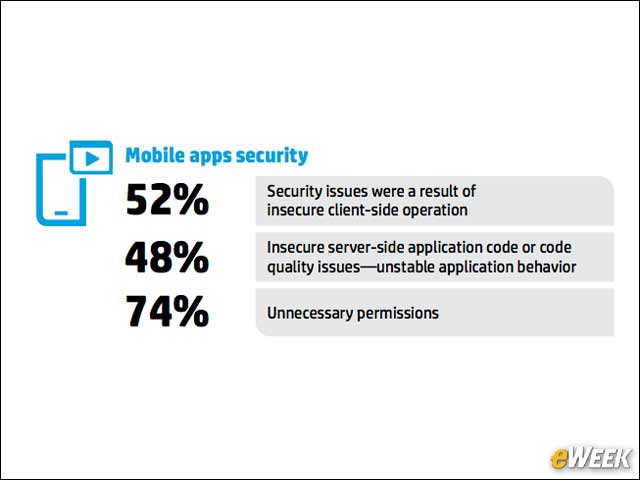
HP’s report also highlights mobile app security trends and found that 74 percent of apps ask users for unnecessary permissions. More than half of all mobile app security issues were attributed to insecure client-side (as opposed to server-side) operations.
Encryption: The Leading Mobile App Security Issue
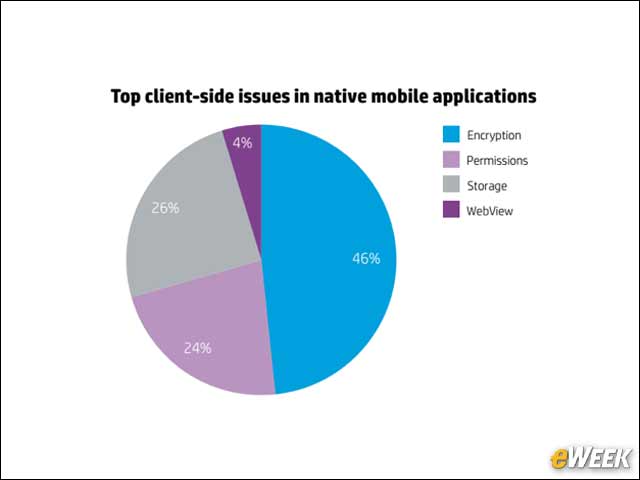
Looking into the root causes of the mobile app client-side issues, HP found that 46 percent of apps do not use or properly implement encryption.
Trojans Dominate the Android Malware Landscape
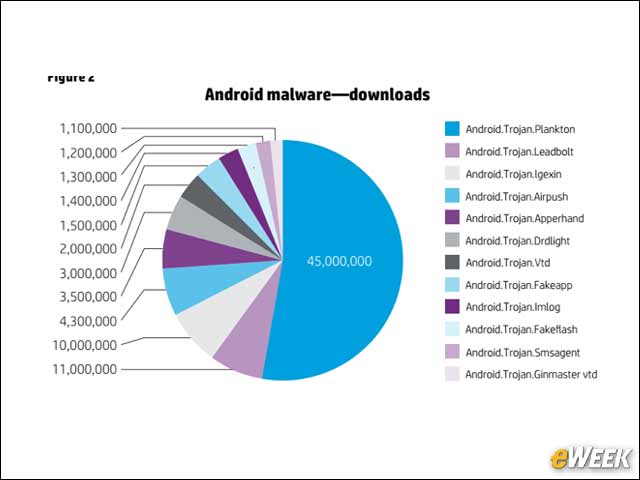
When it comes to Android malware, Trojans are dominant and, in particular, HP found that the “Plankton” Android Trojan was the most downloaded in 2013.
Software Is Leaking Information
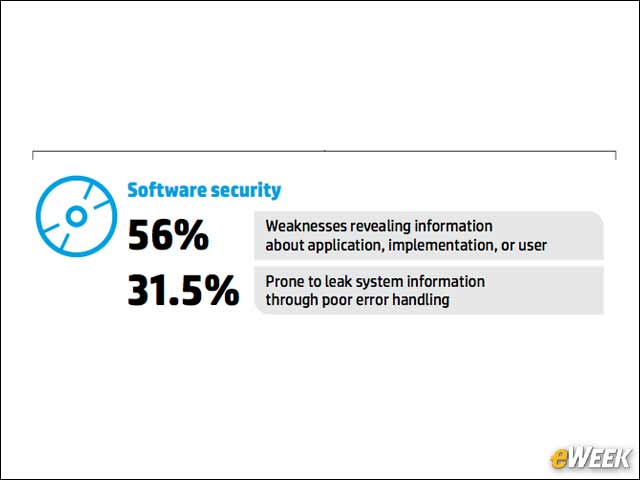
Although there are multiple avenues that an attacker can take to exploit a user or enterprise, HP found software security, in general, to be somewhat lacking with more than half of all applications with weaknesses that provide information that an attack could potentially leverage.








