- Verizon Puts Data Breaches, Attack Patterns Under Microscope
- Attack Patterns Vary by Industry
- Server Breaches More Common Than User Device Breaches
- Law Enforcement Discovering More Breaches
- Web App Attacks Are Growing
- Crimeware Is Often Discovered Within Seconds
- Most Cyber-Espionage Is State-Affiliated
- Cyber-Espionage Comes Largely From Eastern Asia
Verizon Puts Data Breaches, Attack Patterns Under Microscope
by Sean Michael Kerner
Attack Patterns Vary by Industry
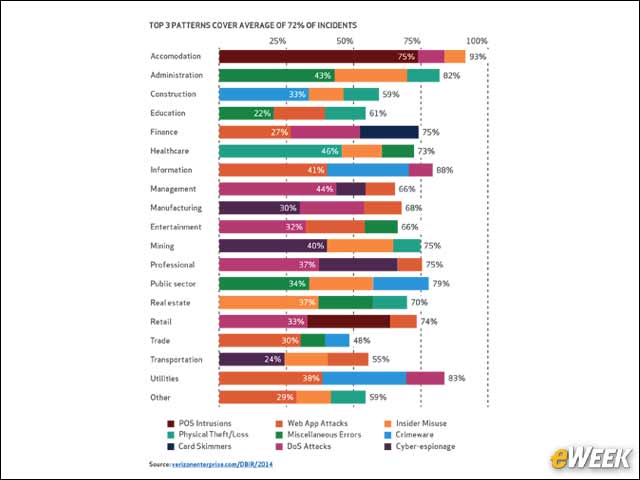
The Verizon 2014 DBIR illustrates that attack patterns vary by industry. In the accommodation industry, for instance, 75 percent of attacks came by way of point-of-sale (POS) intrusions.
Server Breaches More Common Than User Device Breaches
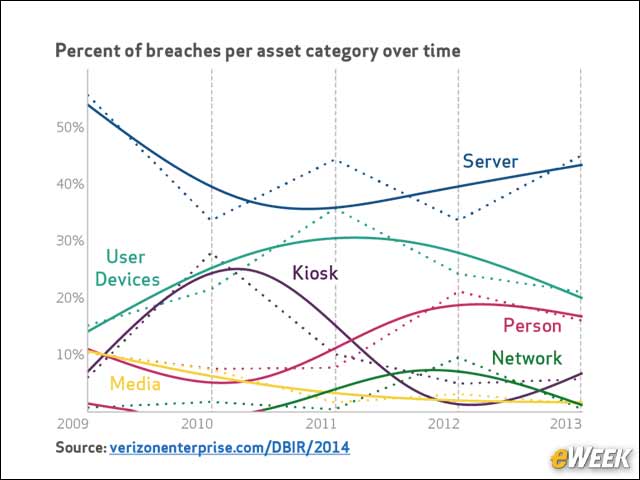
The Verizon 2014 DBIR examined the percent of breaches per asset category over time and found a steady trend of server breaches over the last five years.
Law Enforcement Discovering More Breaches
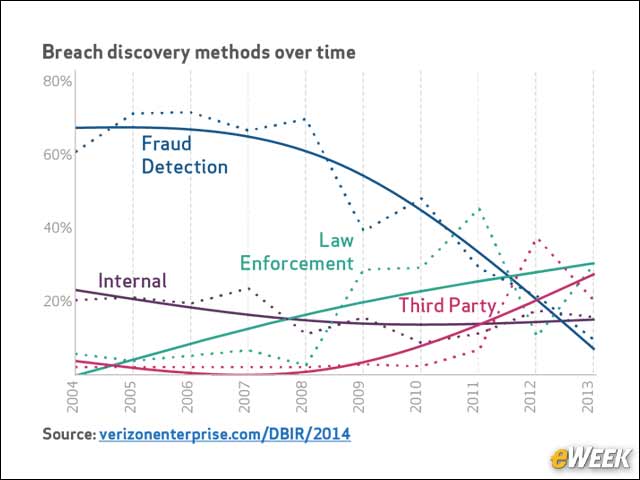
Over the last 10 years, the breach discovery methods have changed positions, with fraud detection going from first to last and law enforcement going from last to first.
Web App Attacks Are Growing
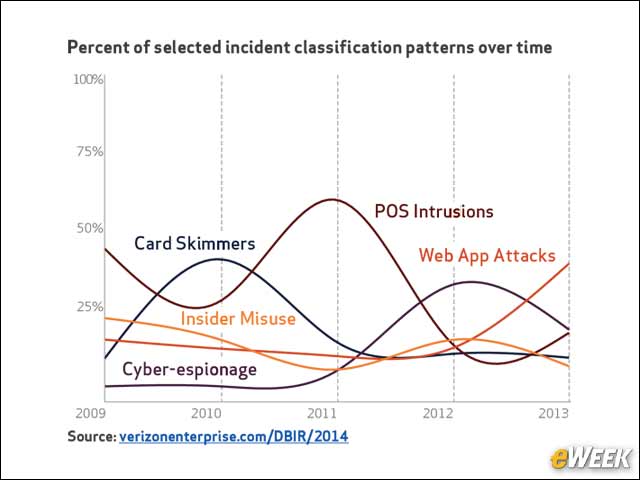
Over the last five years, the Verizon DBIR shows an increase in Web app attacks.
Crimeware Is Often Discovered Within Seconds
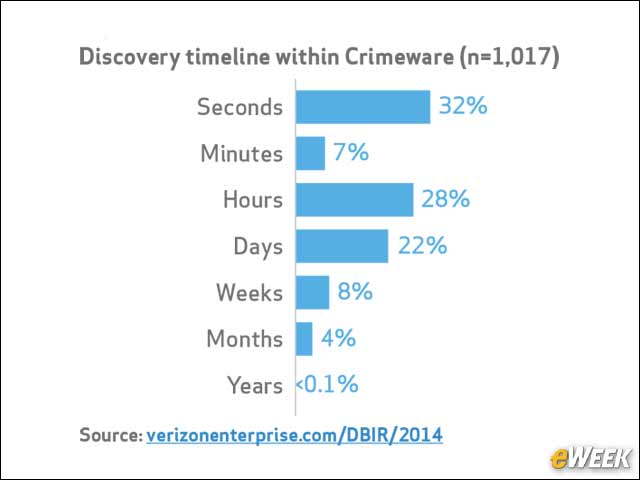
Crimeware is among the attack patterns analyzed in the 2014 DBIR. Overall, Verizon had 12,535 reported incidents of crimeware in 2013, with only 50 having a confirmed data disclosure. The discovery timeline for crimeware was rapid, with 32 percent of incidents detected within seconds.
Most Cyber-Espionage Is State-Affiliated
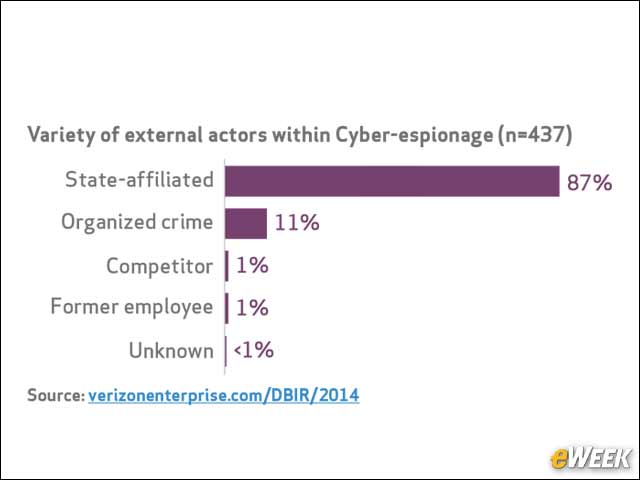
The Verizon 2014 DBIR analyzed 511 total incidents of cyber-espionage, of which 306 had confirmed data disclosure. In fact, 87 percent of all cyber-espionage incidents analyzed by the DBIR were state-affiliated.
Cyber-Espionage Comes Largely From Eastern Asia
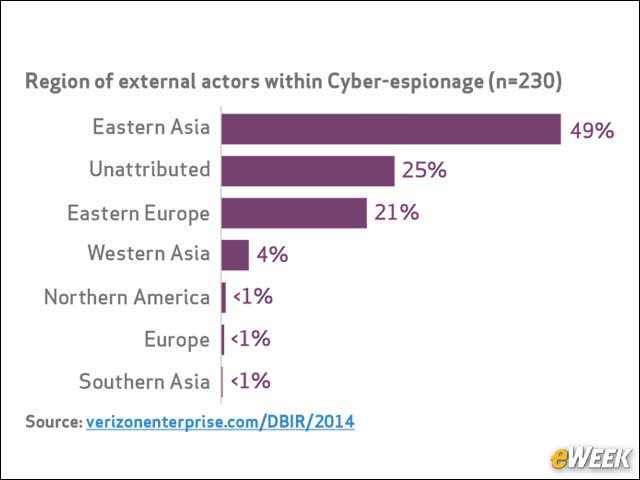
The 2014 DBIR found that Eastern Asia, which includes China and Korea, was responsible for 49 percent of reported incidents.








