- Why Backoff Malware Is Such a Big Threat to Retailers
- Backoff Has Been Active Since October 2013
- At Least 1,000 Businesses Across the U.S. Have Been Infected
- Backoff Targets Windows POS
- Remote Desktop Software Is the Point of Entry
- Java Is an Indicator of Compromise
- Magnetic Stripe Credit Card Data Is Easily Stolen
- Backoff Has Keylogging Features
- Backoff Communicates Credit Card Data Every 60 Seconds
- Proper Security Can Limit Backoff Risk
Why Backoff Malware Is Such a Big Threat to Retailers
by Sean Michael Kerner
Backoff Has Been Active Since October 2013
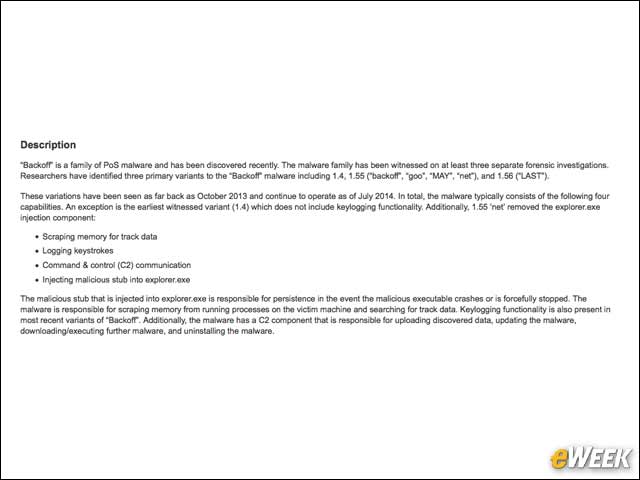
Although the U.S. government didn’t issue a public advisory about Backoff until July, it turns out the malware has been active since October 2013.
At Least 1,000 Businesses Across the U.S. Have Been Infected

Initially, 600 businesses were thought to be at risk from Backoff, but that number has been revised upward to “at least” 1,000, according to US-CERT.
Backoff Targets Windows POS
Trustwave’s Karl Sigler notes that Backoff works against any Microsoft Windows-based POS system.
Remote Desktop Software Is the Point of Entry
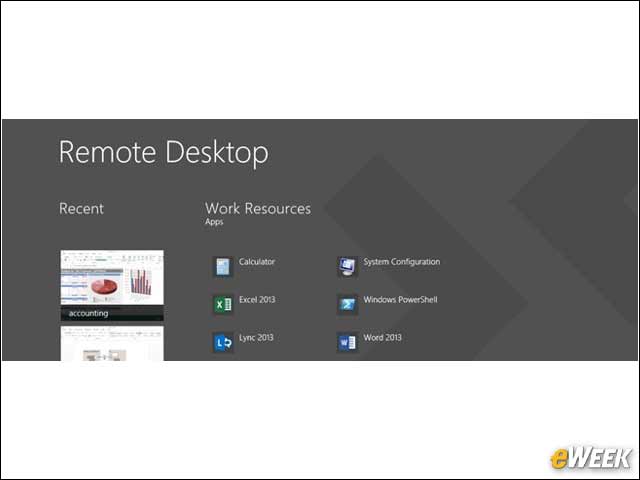
In most cases, the initial breach into a retailer’s POS system is by way of some form of Remote Desktop Protocol (RDP) access.
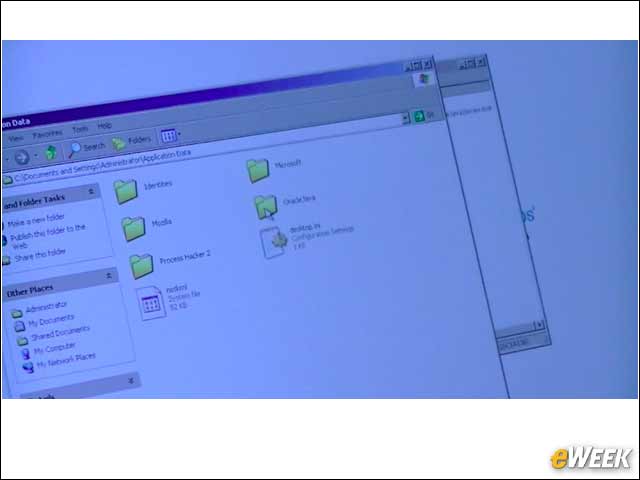
Java Is an Indicator of Compromise
Sigler explained that in some cases, when the Backoff malware lands on a system, it is installed to an Oracle Java directory with an executable name of javaw.exe. He added that most POS systems typically don’t need to have Java.
Magnetic Stripe Credit Card Data Is Easily Stolen

One of the core capabilities of Backoff is that it grabs customer credit card data taken from magnetic stripe card swipes.
Backoff Has Keylogging Features
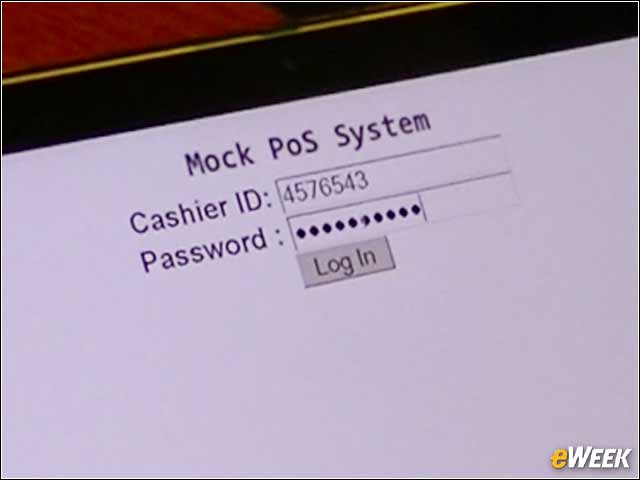
Going a step beyond just card swipes, Backoff also has keylogging features. Sigler noted that even if a cashier manually enters a credit card number, that data will also be compromised.
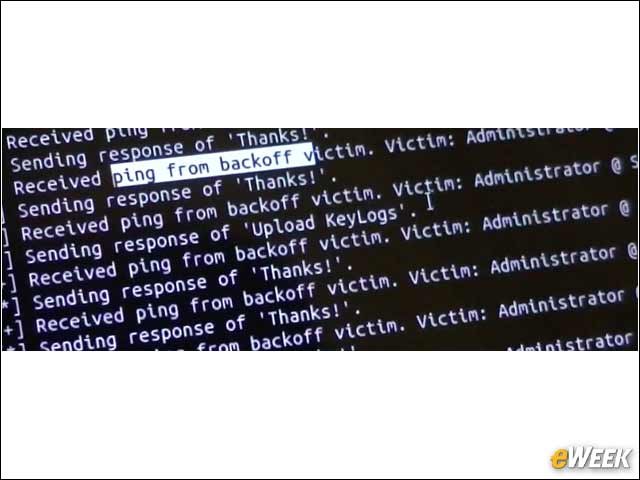
Backoff Communicates Credit Card Data Every 60 Seconds
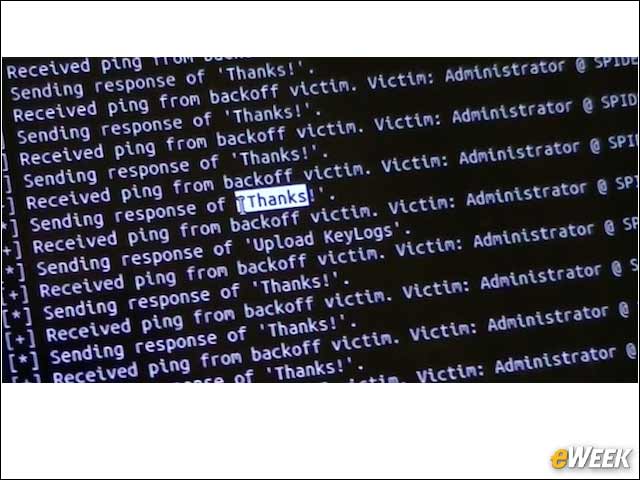
An infected Backoff system can communicate stolen data back to a command and control host every 60 seconds.
Proper Security Can Limit Backoff Risk
Sigler suggests that retailers have a firewall in place that monitors for communications to rogue servers. The use of strong passwords and two-factor authentication is recommended as well. Reducing the attack surface by properly securing remote desktop access can also reduce the risk.








