eWEEK content and product recommendations are editorially independent. We may make money when you click on links to our partners. Learn More.
1TopSpin Security’s DECOYnet Uses Deception to Defend Networks
Many IT security professionals have come to rely on perimeter defense technologies in an effort to prevent attacks. However, as demonstrated by continual corporate data breaches, traditional security measures even when properly implemented, have come up short, attacks undetected and critical data exposed. Simply put, how can the IT department protect business assets if hackers are able to penetrate perimeter defenses undetected? Herzliya, Israel based TopSpin Security aims to solve that security problem with its DECOYnet platform that is that is designed to protect resources using a different ideology, one of deception. DECOYnet incorporates advanced forensics with extensive traffic gathering capabilities to assist administrators to camouflage their subnets from intruders. DECOYnet uses technology that valid resources, while directing attackers to decoy resources and traps.
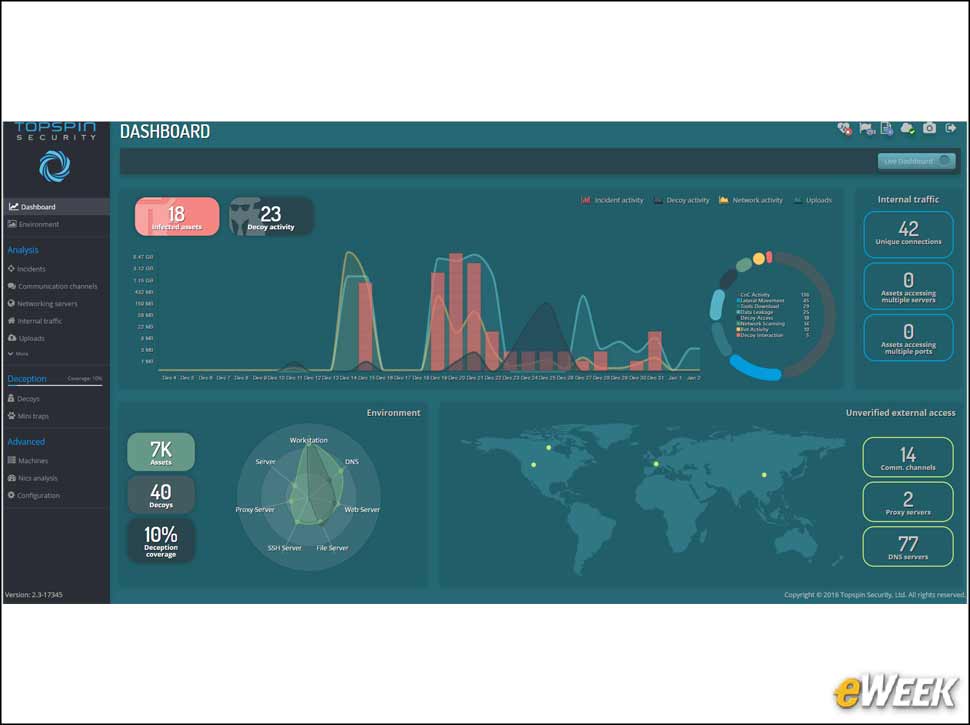
2DECOYnet Dashboard Tracks Suspicious Activity
The dashboard shows summary information about various types of activity detected in DECOYnet. The top part of the window shows a graph view of all the incidents, decoy activity, amount of uploads and network activity (suspicious, but not yet over the threshold) detected in the platform. Red dots on the graph represent infected assets.
3Suspicions Confirmed
4Understanding the Story of Attack
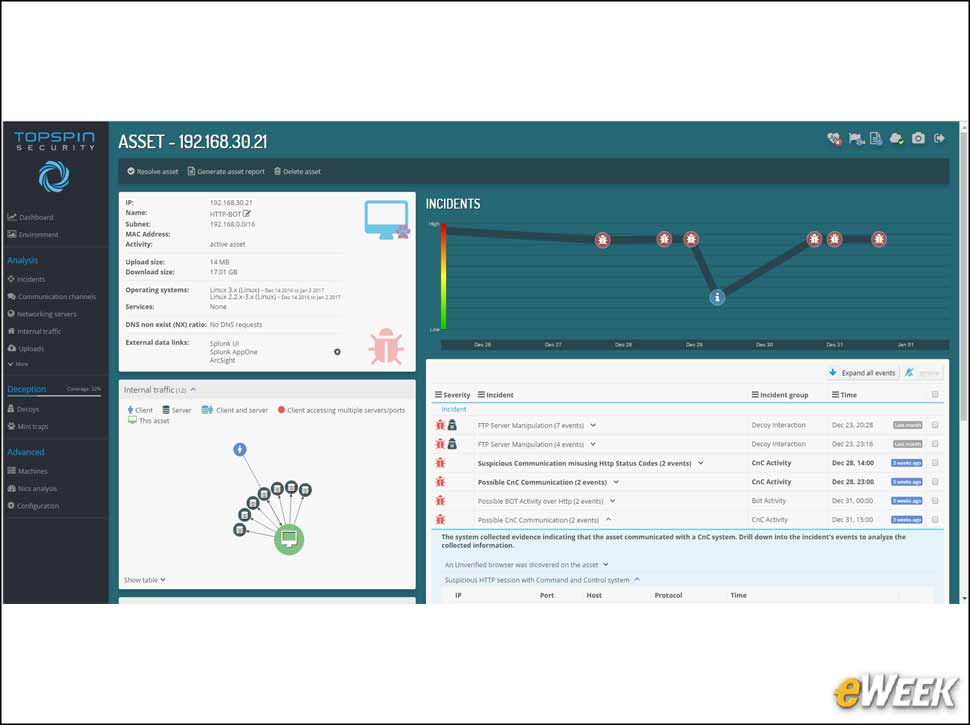
5Investigating Incidents
The Incidents window displays all the relevant incident-related information. Incidents in DECOYnet represent a collection of events, where each event is based on some type of activity in the network, such as accessing or attempting to access a decoy and the command and control communication. Incidents can be shown in order of severity or time of occurrence.
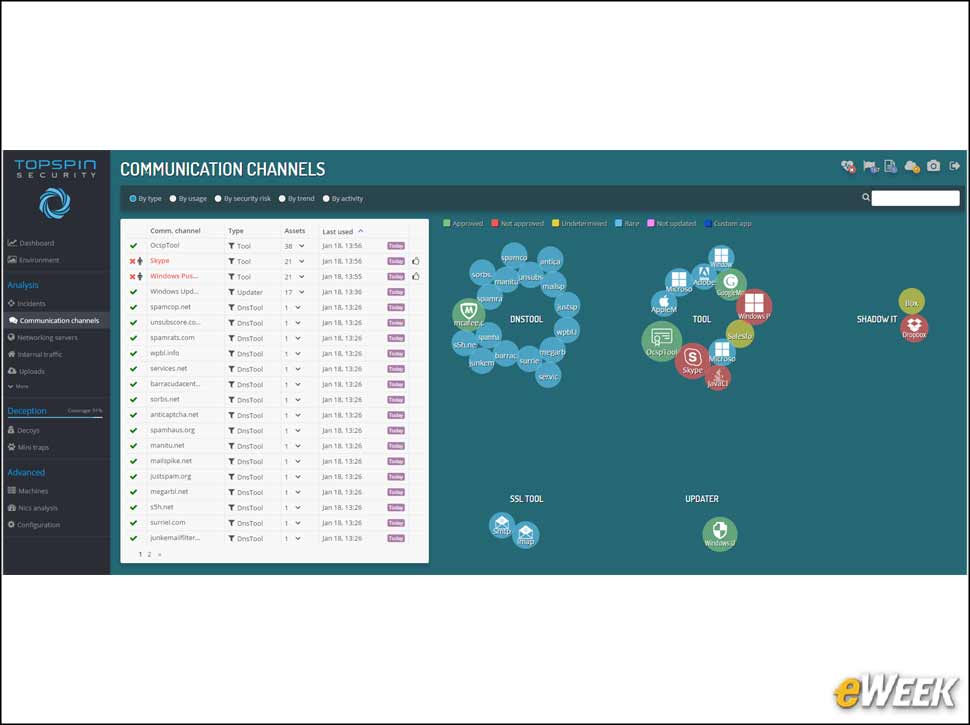
6Forensic Analysis of Internet Connections
The Communications Channels window displays information about the communication that go out of the organization to the Internet. These include anti-virus updates, Windows updates, FTP, Utorrents, shadow IT tools and so on. The channels are color coded as per the level of risk they pose to the organization.
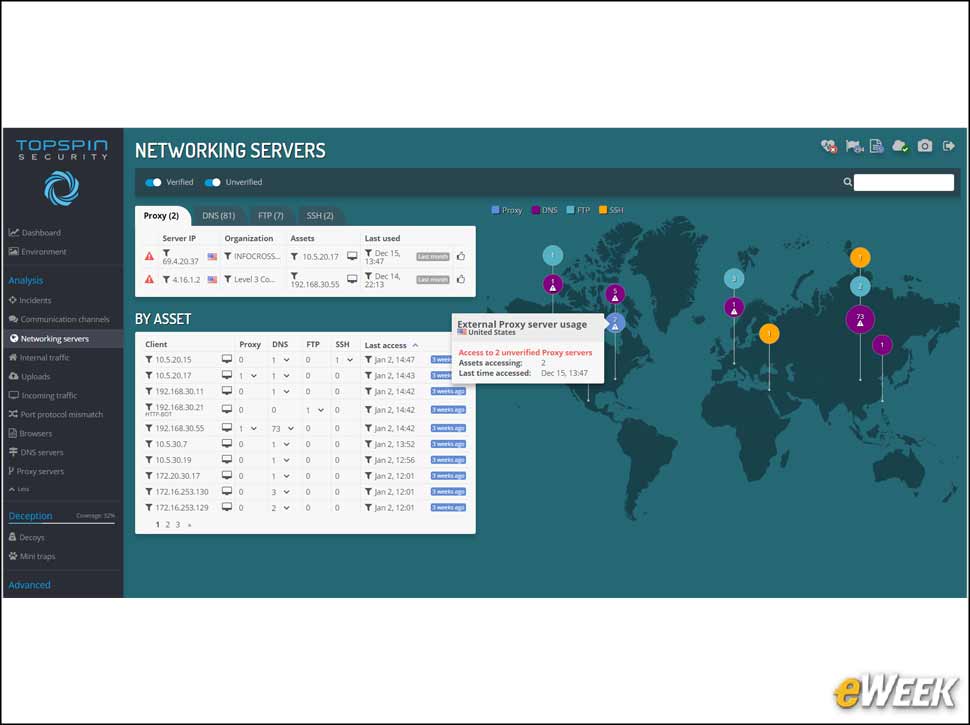
7Know Your Servers
The Networking Servers window displays information about the servers accessed from inside the organization. Each circle represents a different type of server. The size of each displayed circle indicates its associated server’s popularity. The larger the circle the more heavily that server is used in the organization.
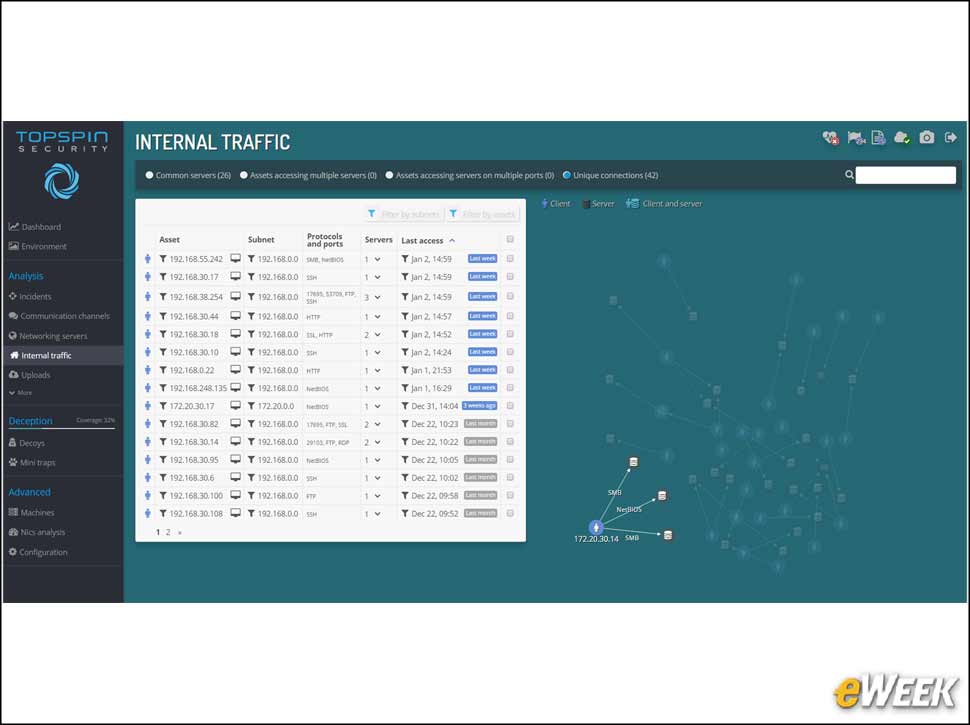
80Mapping and Identifying Internal Traffic
9Detecting Suspicious Upload Activity
10Achieving Optimal Deception Coverage
11There Are Point and Click Configuration Options
DECOYnet’s Adaptive Deception functionality can be easily configured and deployed via the Subnets tab on the Environment window. Enabling adaptive deception on a subnet is done using an intuitive wizard. This wizard defines an entire decoy network and the Mini-Traps the point to it on any subnet. Once enabled, DECOYnet will automatically adjust the deception layer to changing network conditions.