eWEEK content and product recommendations are editorially independent. We may make money when you click on links to our partners. Learn More.
1Verdasys Risk Assessment Program
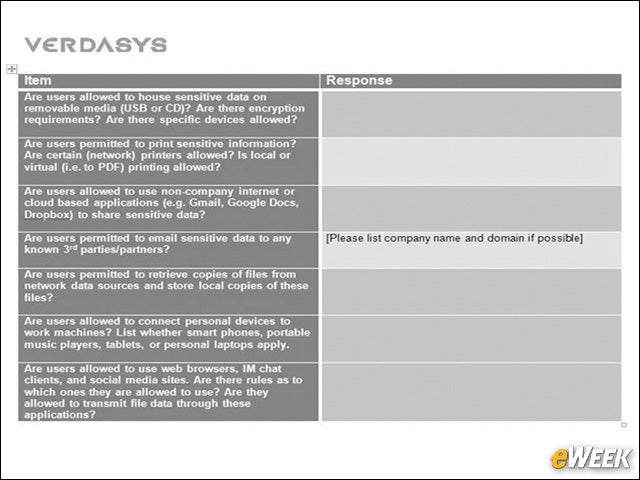
The Verdasys Managed Service Risk Assessment Program begins with a questionnaire which gathers answers to key questions such as “Are users allowed to use Dropbox?” or “Are users allowed to email sensitive data to any known third parties?” The purpose of the questions is to determine if there are pre-existing policies in place.
2Data Loss Protection Service
It’s easier than ever to move sensitive data from an endpoint to removable media such as USBs, iPods and iPhones. Verdasys’ MSIP relies on the Verdasys Digital Guardian DLP solution to provide removable media encryption on data and devices individually by file, device type, brand or model. The customer receives a report like this one detailing who is sending what and where, for a complete audit to meet compliance and forensic needs.
3Controlling Data at All Phases
Capturing hard-to-detect, high-risk user actions such as print and “print screen” information can prohibit the unauthorized movement of confidential information. The MSIP print report shows key information such as file size and type, top users and printers. Many organizations can’t confirm whether valuable data is exposed, let alone how. The MSIP helps them answer the most detailed data security questions. It can even see printing online or offline, from home or work, to local, network and “soft” printers such as PDFs.
4Following Data in Motion
5Validating Data in Emails
6Extensive Reporting
Who is using Dropbox? What are they doing with it? Is a company’s sensitive data at risk of being sent to the cloud unencrypted? It’s important to monitor the usage of risky applications in an environment and determine whether these applications have accessed sensitive data. This report drills down into individual machines and users. It can also show how data is used in a complete usage context, from executive summaries to detailed forensics.
7Role-Based Controls
8Enhanced Views
Understanding acceptable use verses unacceptable use of data is critical in order to enable users to legitimately conduct business. Here you can see that an email was sent to Gmail with work data. Is it safe? Enterprises need to be able to collaborate or allow users to send social email, for example. But what is an acceptable use of these social services? This report allows the MSIP customer to see a full view of activity and flag potentially risky behavior.
9Activity Reporting
10Questionable Business Process Detection
This MSIP report, provided by an actual Verdasys customer with identifying information removed, was provided because it flags a questionable business process—a single executable was uploaded to a host in China and accessed system-level files. This type of activity can be indicative of an Advanced Persistent Threat or some other cyber-threat. It was recommended that the business utility of this process should be reviewed. The response the MSIP team can take may include restricting the application, retrieving all files it touches, cautioning the user of a risky business activity or even shutting down the application.
11Customizable Rules and Policies
Verdasys MSIP engineers work closely with the customer to create rules and policies tuned specifically for each business workflow and process. Robust exception handling capabilities, honed over years of field experience with large Global 2000 companies, are invoked to support complex workflows.